AI Overview:
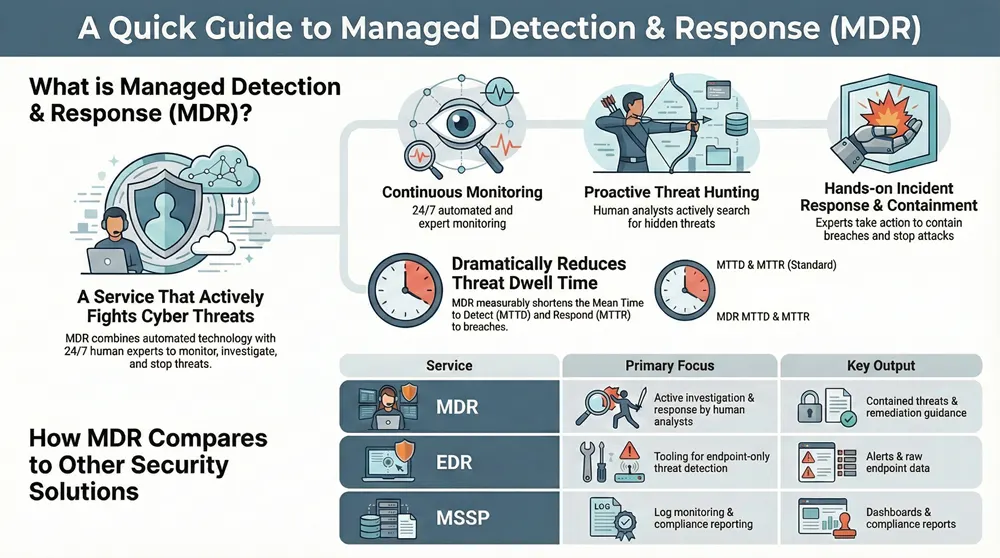
Managed Detection and Response (MDR) is a proactive cybersecurity service that combines continuous telemetry collection, AI-driven analytics, and 24/7 human-led investigation to detect, contain, and remediate threats before they cause major business impact. This blog explains how MDR works across endpoints, networks, cloud, and identity systems; how it differs from EDR tools and MSSPs; and why organizations adopt MDR to reduce dwell time and improve MTTD/MTTR. Readers gain a clear view of MDR’s core components—threat hunting, incident response, and AI-enhanced observability—along with business benefits, industry use cases, and practical criteria for choosing the right MDR provider.
What is MDR? Managed Detection and Response Explained for Effective Cybersecurity
Managed Detection and Response (MDR) is a proactive cybersecurity service that combines continuous telemetry collection, automated analytics, and expert human investigation to detect, contain, and remediate threats before they cause major business impact. This article explains what MDR is, how it works across endpoints, networks, and cloud environments, and why organizations choose managed detection and response to reduce dwell time and improve incident outcomes. Readers will learn the core components of MDR services, how MDR differs from related tools like EDR and services like MSSPs, the role of AI-enhanced observability, industry-specific use cases, and practical selection criteria for choosing a provider
The guide maps danger-to-solution workflows—telemetry → triage → threat hunting → containment—and translates technical capabilities into business metrics such as reduced mean time to detect (MTTD) and mean time to respond (MTTR). Throughout, you’ll see how modern MDR integrates threat intelligence, SOC-level human analysis, and automation to deliver continuous protection and regulatory support. Keywords addressed include MDR services, 24/7 threat hunting, managed detection response, MDR vs EDR, and AI-enhanced observability.
What is Managed Detection and Response in Cybersecurity?
Managed Detection and Response is a service model that pairs automated detection technologies with 24/7 human-led monitoring and active response to identify and stop threats across an organization’s attack surface. It works by ingesting telemetry from endpoints, networks, cloud platforms, and identity systems, applying analytics and machine learning to surface anomalies, and routing prioritized incidents to trained analysts for investigation and containment. The result is faster detection, reduced dwell time, and a coordinated response that combines automated playbooks with human judgment. MDR covers proactive threat hunting, continuous monitoring, incident response, and forensic follow-up, providing organizations with both technical detection capabilities and operational response capacity. Below is a concise summary of core MDR functions for quick reference.
MDR provides three core functions that define its value:
- Continuous 24/7 monitoring to detect anomalous activity across environments.
- Proactive threat hunting to find stealthy or novel intrusions before alerts trigger.
- Incident response and containment to stop active threats and begin recovery.
For organizations evaluating MDR offerings, Concertium positions its MDR capabilities within a broader Collective Coverage Suite that emphasizes proactive 24/7 monitoring and rapid incident response; readers can review provider differentiation later in the article. Understanding how MDR combines automation and human expertise clarifies why many organizations choose managed detection services rather than point tools alone.
How does MDR combine technology and human expertise for 24/7 threat detection?
MDR blends automated sensors, ML/AI analytics, and human analysts to deliver continuous detection and investigation capabilities that scale beyond what either approach can achieve alone. Telemetry collection—from endpoints, network sensors, cloud logs, and identity systems—feeds analytics that prioritize risky behavior and surface high-fidelity alerts, while human analysts perform context-rich triage, enrichment, and threat hunting. This workflow typically moves from telemetry ingestion to alert enrichment, then to analyst-led investigation and containment actions, ensuring automated signals are validated and false positives are minimized. The human element also adapts playbooks, interprets attacker intent, and escalates incidents through defined response channels, preserving oversight and accountability. By combining both, MDR sustains 24/7 threat detection while keeping complex decisions in human hands.
What are the core components of MDR services including threat hunting and incident response?
MDR services are composed of discrete but interconnected capabilities that deliver detection-to-response coverage and continuous improvement for security posture. Core components include telemetry ingestion and normalization, machine-assisted detection and alerting, proactive threat hunting, incident response and containment, forensic analysis and root cause investigation, and vulnerability/prioritization insights that feed remediation guidance. These components reduce dwell time, support compliance reporting, and provide operational playbooks for coordinated containment. Below is a compact mapping of primary MDR components to their functions and business value.
The primary MDR components are summarized in the following operational table.
This mapping clarifies how each capability converts technical activity into measurable business protection, informing procurement and operational decisions. The next section explains how MDR differs from adjacent tools and service models.
How Does MDR Differ from Other Cybersecurity Services Like EDR and MSSP?
MDR is distinct from Endpoint Detection and Response (EDR) tools and Managed Security Service Providers (MSSPs) because it combines active response, human-led investigation, and multi-layer visibility rather than only providing a tool or log-monitoring service. Unlike EDR products that are primarily agent-based detection tools focused on endpoints, MDR treats detection as an operational service that includes analysts who investigate alerts and execute containment. MSSPs often provide log aggregation, rule-based monitoring, and compliance reporting, but may not offer proactive threat hunting or the same depth of incident response. MDR therefore sits between tools and broad managed services, delivering outcome-oriented SLAs and demonstrable reductions in dwell time. The comparison below summarizes these differences for quick evaluation.
To clarify buyer expectations, compare the service models directly in this structured view.
This contrast shows MDR’s operational focus on active detection and human-driven response versus EDR’s tooling orientation and MSSP’s monitoring/compliance orientation. For organizations needing broader coverage, MDR typically integrates EDR/XDR telemetry and augments those tools with analyst-led hunting and response.
What are the key differences between MDR, Endpoint Detection and Response, and Managed Security Service Providers?
Choosing between MDR, EDR, and MSSP requires understanding ownership of response, coverage expectations, and the level of human involvement organizations require for effective defense. EDR provides raw endpoint visibility and automated local responses but requires in-house expertise for complex investigations and cross-environment correlation. MSSPs provide centralized log monitoring and compliance support but often lack deep threat hunting and rapid containment capabilities. MDR vendors accept operational responsibility for detection and response, offering SOC-level analysts, playbook-driven containment, and integration across endpoints, cloud, and network data. This difference matters when an organization lacks internal SOC resources or needs guaranteed response SLAs tied to business outcomes.
How does MDR provide broader coverage across endpoints, networks, and cloud environments?
MDR extends visibility by aggregating telemetry from multiple sources—EDR agents on endpoints, network sensors, cloud workload logs, identity systems, and SaaS application telemetry—then correlating events to reveal multi-stage attacks. Integration layers and normalization permit analytics to link a suspicious login in cloud identity logs to lateral movement on endpoints and anomalous data flow on the network, enabling faster and more accurate detection. Cross-layer correlation frequently uncovers attacker techniques that single-source tools miss, such as credential stuffing leading to data exfiltration via cloud storage. This broader coverage enables MDR teams to interrupt attack chains earlier and reduce the likelihood of costly breaches.
Further research highlights the importance of multi-layered security frameworks in addressing complex, hybrid attack scenarios across diverse environments.
Multi-Layered Real-Time Security Framework for Threat Detection
To address these challenges, we propose SFARP, a multi-layered real-time security framework tailored for SD-IoT environments. SFARP integrates three coordinated modules: (1) the Dynamic Flow Analysis Module (DFAM), which leverages P4-programmed switches to extract fine-grained traffic and ARP-level features; (2) the Adaptive Dynamic Flow Detection System (ADFDS), which employs an ensemble of machine learning classifiers to detect anomalies across hybrid and multi-vector attack scenarios; and (3) the Distributed Adaptive Mitigation System (DAMS), which deploys adaptive countermeasures across a multi-controller SDN topology.
SFARP: a multi-layered real-time security framework for hybrid ARP and DDoS attack defense in SD-IoT networks, A El-Sayed, 2025
What Are the Benefits of Implementing MDR Solutions for Businesses?
MDR transforms technical detection capabilities into measurable business outcomes by reducing risk exposure, lowering incident costs, and supporting compliance. The most frequent business benefits include reduced mean time to detect and respond, predictable operational security costs compared to building an in-house SOC, enhanced regulatory evidence and reporting, and continuous improvements from threat intelligence and lessons learned. Organizations see value not only in faster containment but also in the reduction of operational overhead—MDR replaces the need to recruit, train, and retain specialized analysts while delivering enterprise-grade processes. Below is a direct list of top business benefits with one-line metrics to illustrate impact.
Businesses achieve several measurable benefits from MDR:
- Faster detection and response, typically cutting MTTD/MTTR by measurable percentages through continuous monitoring and analyst triage.
- Lower operational costs by outsourcing SOC capabilities and avoiding CAPEX tied to tooling and staffing.
- Regulatory support and defensible reporting to satisfy frameworks such as HIPAA, PCI DSS, and similar standards.
- Reduced breach impact through proactive hunting and rapid containment, decreasing potential remediation expenses.
To translate these into concrete decision criteria, the following table links benefits to typical metrics and business impacts.
These outcomes show how MDR converts technical defenses into financial and operational advantages. For example, Concertium’s Collective Coverage Suite (3CS) couples AI-enhanced observability with 24/7 monitoring and rapid incident response to deliver many of these business benefits as part of an an end-to-end managed offering.
How does MDR reduce cybersecurity risks and improve incident response times?
MDR reduces risk by shortening the window attackers can operate inside an environment through continuous monitoring, prioritized alerts, and analyst-driven containment. Automated detection surfaces suspicious behavior, while human analysts validate and enrich alerts to avoid chasing false positives and to focus on high-risk incidents. Proactive threat hunting finds stealthy adversaries that evade rules-based systems, and playbook-driven containment speeds remediation actions across environments. The combined effect is demonstrable reduction in dwell time and faster resolution—metrics organizations use to justify MDR investment.
In what ways does MDR support regulatory compliance and cost savings for business owners?
MDR supports compliance by generating structured forensic artifacts, maintaining chain-of-custody evidence, and delivering timely incident reports required by regulations such as HIPAA and PCI DSS. Outsourcing detection and response converts unpredictable capital investments into predictable operational expense, eliminating costs associated with hiring, training, and retaining scarce security talent. MDR providers also augment existing controls with advisory services to close compliance gaps and help prepare for audits. The result is lower total cost of ownership and stronger audit readiness without adding heavy internal staffing burdens.
How Does AI-Enhanced Advanced Observability Improve MDR Capabilities?
AI-enhanced observability enriches MDR by improving signal-to-noise ratio, accelerating triage, and enabling anomaly detection across diverse telemetry at scale. Machine learning models baseline normal behavior, surface deviations that indicate compromise, and automatically enrich alerts with contextual threat intelligence to speed analyst decisions. AI also prioritizes alerts by risk and can trigger automated containment playbooks for common, high-confidence scenarios, freeing analysts to focus on complex investigations. However, human oversight remains critical: analysts validate AI findings, resolve ambiguous cases, and refine models through feedback loops to prevent over-reliance on automation. Together, AI and human analysts create more efficient and accurate managed detection and response workflows.
The concept of cloud observability is further explored as a critical component for proactive incident management, emphasizing its role in generating meaningful insights from data.
Cloud Observability for Proactive Incident Management
Cloud computing has revolutionized the way organizations deploy, manage, and scale their infrastructure. But the heterogeneous and dynamic nature of the cloud environment poses a great challenge to how to maintain the reliability availability and performance of the system. Conventional monitoring systems gazed at the information and responses based on the certain limits, while the idea was to capture the problems after they impacted the services. Cloud architectures have evolved drastically since then, and this method has started to fall short, as it demands real time visibility and proactive management to address service interruptions and optimize operational efficiency. Cloud observability is one of the key concepts that has come into play to overcome the limitations of conventional log analysis, as it allows for a data-driven, thorough approach to monitoring by generating meaningful insights from the data.
Cloud observability: Ai-enhanced monitoring for proactive incident management-2025, S Banala, 2025
To show concrete AI roles, consider the following list that outlines primary AI-supported functions in MDR.
- Alert Prioritization: AI ranks incidents by risk to reduce analyst workload and focus on high-impact events.
- Anomaly Detection: Machine learning identifies deviations from baseline behaviors across large telemetry volumes.
- Enrichment & Correlation: AI aggregates threat intelligence and contextual data to speed investigations.
AI-powered observability therefore increases analyst productivity and detection fidelity, but it must be paired with explainable models and human review to maintain trustworthy operations.
What role does artificial intelligence play in proactive threat detection and alert filtering?
AI plays three practical roles in MDR: reducing false positives through pattern recognition, detecting anomalies that rules miss, and enriching alerts with relevant context like indicators of compromise. By correlating signals across endpoints, network, and cloud telemetry, ML models uncover multi-stage attack patterns and prioritize those with the greatest business risk. AI reduces time spent on low-value alerts, enabling analysts to close incidents faster and focus threat hunting on emerging adversary behaviors. Explainability and feedback loops are essential so analysts can tune models and ensure automated actions align with organizational risk tolerances.
How does AI assist human analysts in managing complex cybersecurity threats?
AI augments analysts by providing context enrichment, automated IOC (indicator of compromise) lookups, attack path visualization, and suggested containment steps based on historical playbooks. During investigations, AI can surface related events, map lateral movement, and estimate likely impact, enabling analysts to make faster, evidence-based decisions. Automated playbooks can execute containment for common high-confidence incidents while leaving complex, high-risk decisions to experts. This human-plus-AI workflow accelerates resolution while preserving oversight, ensuring that sophisticated threats receive the depth of human analysis they require.
Research into human-AI collaboration further emphasizes the strategic integration of AI agents to augment SOC effectiveness and manage the increasing complexity of cyber threats.
Human-AI Collaboration for Augmented Cybersecurity Operations
Abstract Security Operations Centres (SOCs) face mounting cognitive and operational demands as cyber threats increase in scale and complexity. This paper proposes a human-AI collaboration framework to augment SOC effectiveness through cognitive profiling and agentic coordination. We map 29 core SOC functions across three cognitive dimensions, thinking mode, attention level, and coordination context, revealing a concentration of tasks in cognitively saturated zones requiring slow thinking, high attention, or collective decision-making. To address these challenges, we introduce a multi-agent architecture grounded in the Belief–Desire–Intention (BDI) model and structured by an extended VOWEL+U framework that embeds human oversight into agentic ecosystems. We define four AI agent roles, Assistant, Auto-Pilot, Companion, and Operator, aligned with operational autonomy levels to support function-specific delegation.
Symbiotic Human–AI Collaboration For Augmented Cybersecurity Operations, R Yaich, 2025
What Are Industry-Specific Use Cases and Applications of MDR Services?
MDR adapts to industry-specific threats and regulatory demands by tailoring telemetry sources, detection rules, and incident playbooks to the risk profile of financial services, healthcare, manufacturing, and other sectors. In financial services, MDR focuses on fraud indicators, transaction anomalies, and insider threats with rules and hunting hypotheses tuned for monetary systems. Healthcare MDR emphasizes protection of protected health information (PHI), rapid breach containment, and support for HIPAA-required notifications. Manufacturing MDR must bridge IT/OT visibility to detect attacks targeting operational technology and prevent production disruption. Industry-specific MDR deployments combine domain knowledge with threat intelligence to deliver relevant detection and response outcomes.
This section lists typical use cases per industry to illustrate practical MDR applications.
- Financial services: Detect anomalous transaction patterns and credential misuse to prevent fraud and lateral movement.
- Healthcare: Monitor access to PHI and quickly contain exfiltration risks while supporting regulatory reporting obligations.
- Manufacturing: Correlate IT and OT telemetry to identify malware targeting industrial control systems and prevent downtime.
How does MDR address cybersecurity challenges in financial services, healthcare, and manufacturing?
In financial services, MDR hunts for lateral movement following credential compromise and integrates transaction monitoring to prioritize threats with monetary impact. In healthcare, MDR emphasizes rapid containment of PHI exposure, maintains forensic evidence for regulators, and reduces recovery time after ransomware or data breaches. For manufacturing, MDR correlates IT logs with OT sensor data to spot anomalies that could disrupt production lines, enabling coordinated interventions that prevent safety and operational impacts. These targeted approaches reduce sector-specific risks and help maintain regulatory compliance and business continuity.
What are real-world examples of MDR reducing breach impact and improving security posture?
Anonymized use-case sketches illustrate MDR outcomes: a financial institution discovered a stealthy credential reuse campaign through cross-source correlation, enabling containment before fraudulent transfers occurred; a healthcare provider reduced time-to-containment for a ransomware incident by leveraging pre-approved containment playbooks and preserved forensic evidence for regulatory reporting; a manufacturer detected lateral movement between corporate IT and an OT management system and removed the adversary before process disruption. Across these examples, MDR reduced dwell time, limited operational impact, and provided clear evidence trails that aided compliance and post-incident remediation.
How to Choose the Right MDR Provider for Your Business Needs?
Selecting an MDR provider requires a structured evaluation of coverage, response capability, transparency, and alignment to business risk. Key criteria include the breadth of telemetry supported (endpoints, network, cloud, identity), clarity of response SLAs and escalation processes, evidence of human analyst capability and threat hunting cadence, reporting and compliance support, and integration flexibility with existing tooling. Providers should demonstrate how they convert detections into actions and provide measurable outcomes such as MTTR improvements and example case studies. The checklist below gives vendor questions and red flags to guide procurement conversations.
Use this checklist during vendor evaluation to ensure comprehensive coverage and operational fit.
- Does the provider support endpoints, network, cloud workloads, and identity telemetry for cross-layer correlation?
- Are response SLAs, escalation paths, and containment authorities clearly defined and contractually supported?
- Can the provider produce forensic artifacts and compliance reporting to meet your regulatory needs?
Applying this checklist helps organizations avoid vendors that only offer tooling without operational response or those that lack integration with critical telemetry sources. The next subsection highlights specific provider differentiators and practical negotiation points.
What criteria should business owners consider when selecting an MDR service provider?
Business owners should prioritize coverage scope, demonstrable analyst expertise, transparent SLAs, evidence of threat-hunting methodologies, integration capabilities with existing EDR/XDR and cloud tooling, and compliance support. Request playbook examples, ask about escalation paths to on-call response teams, and evaluate reporting cadence and content to ensure it satisfies internal and regulatory stakeholders. Red flags include vendors that cannot show case examples of containment outcomes, vendors that rely solely on automated alerts without analyst validation, or those with opaque pricing tied to high implementation overhead. A structured vendor scorecard helps quantify fit against business needs.
How does Concertium’s Collective Coverage Suite and MDR offering stand out?
Concertium’s Collective Coverage Suite (3CS) combines AI-enhanced advanced observability with managed detection and response to deliver end-to-end cybersecurity, risk, and compliance solutions. The suite emphasizes proactive 24/7 monitoring and rapid incident response, automated threat detection and elimination, and a layered security approach that includes post-breach services and compliance advisory. Concertium presents these capabilities alongside advisory services to translate technical detection into business risk reduction and regulatory readiness. For organizations seeking an integrated provider, Concertium positions its MDR as a core component of a broader managed cybersecurity program, and interested leaders are encouraged to talk to an expert at Concertium to discuss tailored coverage and next steps.
- Integrated Observability and Response: Concertium pairs advanced telemetry correlation with analyst-led response.
- Managed Incident Outcomes: The focus is on reducing dwell time and delivering rapid containment.
- Compliance and Advisory Services: Post-breach support and regulatory guidance help complete the protection lifecycle.
This provider-focused summary is intentionally concise and placed where procurement conversations commonly occur; it represents roughly the permissible business integration portion of the article while keeping the primary focus on the MDR topic.
- Talk to an Expert: Organizations evaluating MDR should engage providers to review telemetry needs, SLA expectations, and integration requirements to ensure the chosen service delivers measurable risk reduction.
This final commercial note preserves the article’s educational focus while offering a clear next step for readers who want guided vendor conversations.