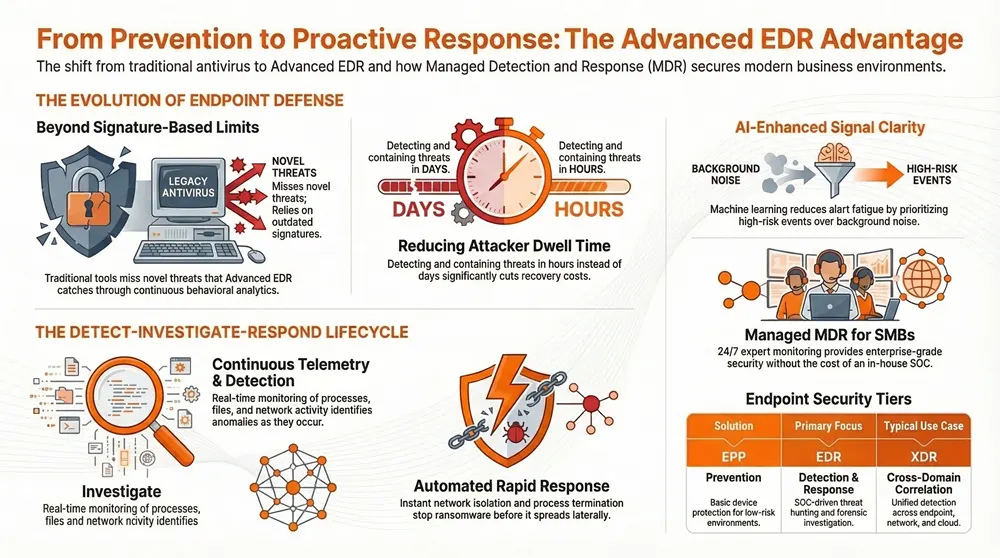
Advanced Endpoint Detection and Response (EDR) is a set of tools and processes that continuously watch devices, surface suspicious behavior, and coordinate investigation and remediation. This guide shows how Advanced EDR reduces operational risk, shortens attacker dwell time, and helps meet compliance goals while fitting into modern managed security operations. Organizations facing sophisticated threats need more than signature-based antivirus; Advanced EDR gives teams the visibility and control to protect endpoints, data, and business continuity.
You’ll learn how EDR differs from legacy protection, how AI-powered observability improves detection, why XDR and EDR serve different needs, and how managed services like Managed Detection & Response (MDR) deliver better outcomes. We also cover practical steps for automated real-time response and an SMB-focused section on affordable adoption. Key terms — endpoint protection, device security, threat hunting, automated remediation — are defined and tied to decisions security leaders make every day.
What is Advanced Endpoint Detection and Response and Why Does Your Business Need It?
Advanced EDR continuously collects endpoint telemetry, applies behavioral analytics and threat intelligence, and coordinates investigation and remediation so you stop threats earlier and with more confidence.
It relies on telemetry from processes, files, and network activity, builds behavioral baselines, and uses analytics to surface anomalies signature-based tools miss — enabling faster detection and more accurate response.
That translates into shorter time-to-detection, automated containment that limits lateral movement, and richer forensic context to support incident response and compliance.
Research and industry data consistently show that reducing dwell time by hours or days cuts breach impact and costs. Advanced EDR is a practical control that achieves those reductions.
Below are the core EDR functions that deliver these business benefits and set the stage for comparing EDR with other endpoint approaches.
Advanced EDR provides three essential functions for modern security operations:
- Detect: Continuous telemetry and behavioral analytics identify anomalous endpoint activity as it happens.
- Investigate: Context-rich forensics connect processes, users, and files so analysts can triage fast.
- Respond: Automated containment, quarantine, and remediation limit spread and speed recovery.
These capabilities explain why organizations add EDR when modern threats bypass signature defenses, and they lead naturally into how EDR compares to traditional antivirus and Endpoint Protection Platforms.
How does EDR differ from traditional antivirus and Endpoint Protection Platforms?
EDR shifts the focus from signature-only prevention to continuous behavior-based detection and response orchestration — a fundamental change from classic antivirus and many EPPs.
Where EPP stops known threats using signatures and static heuristics, EDR gathers continuous telemetry, correlates events, and supports active threat hunting to expose novel or living-off-the-land attacks that signatures don’t catch.
That matters because attackers increasingly abuse legitimate tools or exploit zero-days that won’t match a signature. Behavioral detection and endpoint forensics reveal the intent behind those activities.
A brief comparison makes these differences clear and highlights the security outcomes EDR adds to an EPP baseline, preparing you to evaluate specific features and business benefits.
What are the key features and benefits of advanced EDR solutions?
Advanced EDR combines several interlocking capabilities — telemetry collection, threat hunting, behavioral analytics, automated containment, and forensic investigation — to deliver measurable outcomes like lower breach costs and faster remediation.
Telemetry captures raw signals from processes, files, and network activity; analytics score anomalies and prioritize high-risk events; human threat hunters validate complex attacks; and automated remediation contains threats quickly while preserving evidence for deeper response.
Below is a concise feature-to-benefit mapping to help decision-makers weigh trade-offs and understand practical coverage.
Advanced EDR feature comparison:
This mapping shows how each technical capability converts to operational value and why EDR is more than an incremental upgrade over signature-based protection. From here, we’ll cover how managed detection services put EDR into practice at scale.
How Does Concertium’s Managed Detection and Response Enhance Endpoint Security?
Concertium’s Managed Detection & Response (MDR) operationalizes Advanced EDR telemetry with 24/7 monitoring, human-led threat hunting, and incident response workflows so your team gets continuous protection without adding headcount.
We pair automated analytics with SOC analyst validation so alerts are triaged accurately, prioritized by impact, and escalated under agreed SLAs.
Our Collective Coverage Suite (3CS) combines MDR with AI-enhanced observability and automated threat elimination to reduce blind spots and shorten time-to-containment.
For organizations that can’t run a full SOC in-house, MDR delivers continuous protection, expert investigation, and coordinated remediation while preserving forensic evidence and supporting compliance needs.
Concertium’s MDR capabilities include continuous telemetry ingestion, prioritized alerts, and analyst-driven hunts that augment automated detection:
- 24/7 Monitoring: Continuous monitoring with high-fidelity alerts and analyst escalation.
- Threat Hunting: Proactive, hypothesis-driven investigations to surface stealthy activity.
- Rapid Response: Coordinated containment and remediation workflows to limit impact.
These managed services translate Advanced EDR outputs into practical incident response, and they lead directly into the monitoring and hunting practices that speed containment.
What 24/7 monitoring and threat hunting capabilities does Concertium’s MDR provide?
Concertium’s MDR emphasizes continuous telemetry analysis, proactive hunting, and documented analyst playbooks to turn noisy signals into validated incidents and clear action items.
Monitoring pipelines normalize endpoint data and use AI-enhanced observability to reduce noise, allowing analysts to focus on high-confidence threats and escalate when needed.
Threat hunting builds on telemetry baselines and MITRE ATT&CK-informed hypotheses to uncover living-off-the-land techniques and lateral movement that simple rules can miss.
This hybrid approach — machine prioritization plus human validation — shortens investigations, improves detection precision, and reduces mean time to containment while preserving business continuity.
Concertium’s operational model blends automated detection with human-led investigation to ensure context-aware decisions and faster remediation, setting up the measurable outcomes discussed next.
How does rapid incident response improve cybersecurity outcomes?
Faster incident response narrows the window attackers have to move laterally, exfiltrate data, or escalate privileges, which directly lowers operational and financial impact.
Incident response follows stages — detection, triage, containment, eradication, recovery — executed via playbooks that prioritize containment while preserving evidence for remediation and compliance reporting.
Shorter time-to-containment correlates with lower recovery cost and reduced downtime, and managed response services help ensure those steps are taken consistently and under SLA.
By combining automated containment with analyst oversight, organizations achieve quicker, safer outcomes that support continuity and regulatory obligations.
With that foundation, let’s examine how AI-enhanced observability augments EDR telemetry and improves detection across environments.
How Does AI-Enhanced Advanced Observability Integrate with EDR for Proactive Threat Detection?
AI-enhanced observability layers machine learning and anomaly detection over EDR telemetry to proactively surface subtle deviations across endpoints, network flows, and applications.
Models learn behavioral baselines, assign anomaly scores, and correlate signals across sources so priority incidents rise above noise with fewer false positives.
Integration points include shared telemetry pipelines, correlated alerting, and automatic enrichment of events with contextual data to speed triage.
The outcome: fewer alerts to review, better signal-to-noise, and earlier discovery of attack patterns — all of which boost security team efficiency and effectiveness.
AI and machine learning support observability use-cases that sharpen detection and prioritization:
- Behavioral Baselining: Models learn normal patterns to flag subtle deviations.
- Alert Prioritization: ML reduces alert fatigue by surfacing the highest-risk events first.
- Cross-signal Correlation: Correlates endpoint and network data to reveal multi-vector attacks.
These capabilities make observability a force-multiplier for EDR, and they lead into a closer look at the ML techniques and monitoring improvements that follow.
What role do AI and machine learning play in anomaly detection and behavioral analytics?
AI and machine learning build statistical models that define normal behavior for users, devices, and applications, enabling systems to flag deviations that suggest compromise.
Supervised and unsupervised models surface anomalous process activity, privilege escalations, and unusual data flows, while scoring mechanisms prioritize the highest-risk events.
That automation reduces low-value triage so analysts can focus on complex investigations and hypothesis-driven hunts.
In practice, AI-enhanced analytics increase sensitivity to stealthy attacks while reducing false positives that consume analyst time.
By improving signal quality and prioritization, ML-driven observability shortens time to action and feeds richer context into incident response workflows.
How does advanced observability improve network and user monitoring?
Advanced observability extends telemetry beyond process and file events to include network flows, user sessions, and cloud activity, giving EDR investigations a broader, clearer context.
Network flow visibility reveals command-and-control attempts and lateral movement; user session data helps attribute actions and detect compromised accounts; cloud telemetry links endpoint events to cloud misuse.
Combining these sources shortens triage time and enables precise containment and root-cause analysis.
That broader visibility improves correlation and speeds resolution, increasing the practical value of an EDR program in complex environments.
With these capabilities in view, next we’ll compare EDR, XDR, and Endpoint Protection Platforms to help you choose the right fit.
What Are the Differences Between EDR, XDR, and Endpoint Protection Platforms?
EDR, XDR, and Endpoint Protection Platforms (EPP) serve related but distinct roles: EPP focuses on prevention at the device, EDR emphasizes detection and response on endpoints, and XDR extends detection and response across multiple telemetry domains for broader correlation.
The primary difference is scope: EPP protects individual devices, EDR investigates and remediates endpoint incidents, and XDR correlates telemetry from endpoints, network, email, and cloud to detect multi-vector campaigns.
Buyers choose among these based on SOC maturity, desired coverage, and integration needs. Smaller teams often prefer managed EDR/MDR, while organizations with many telemetry sources may benefit from XDR orchestration.
The table below offers a concise comparison to help decision-makers match needs to capability and managed options.
This comparison helps buyers align platform choice with staffing, coverage, and integration needs and leads into how XDR extends orchestration beyond endpoint-only approaches.
How does Extended Detection and Response expand beyond traditional EDR?
XDR ingests and correlates signals from additional layers — network telemetry, email gateways, cloud services, identity providers — and enables automated orchestration across attack surfaces.
With a broader telemetry set, XDR links disparate events into coherent attack chains, improving detection of multi-stage intrusions and reducing false positives through cross-source validation.
Orchestration in XDR can automate multi-step containment across systems, accelerating comprehensive response.
This cross-domain approach is especially useful for organizations that need holistic visibility and fast orchestration across diverse environments.
Why is understanding these differences important for selecting the right cybersecurity platform?
Choosing between EPP, EDR, and XDR requires balancing coverage, cost, and staffing. Smaller organizations may favor managed EDR for focused endpoint response, while enterprises with many telemetry sources often invest in XDR to centralize correlation and automation.
Key decision criteria include SOC staffing, integration with existing SIEM or cloud telemetry, compliance needs, and the expected threat profile.
Evaluating those factors helps security leaders pick a solution that delivers the right mix of prevention, detection, and response without overtaxing operations.
A simple buyer checklist can clarify which model fits your readiness and risk appetite.
Next, we’ll look at how SMBs can adopt EDR capabilities within realistic budget and staffing constraints.
How Can Small and Medium Businesses Benefit from Advanced EDR Solutions?
SMBs get outsized value from Advanced EDR because managed detection and automated response deliver enterprise-grade protection without the cost of running a full SOC.
SMBs face phishing, ransomware, and supply-chain risks but often lack continuous monitoring, threat-hunting expertise, and response capacity. EDR plus managed MDR fills those gaps with telemetry-driven detection, analyst validation, and containment workflows.
The result is a stronger security posture with predictable costs, better insurance positioning, and clear compliance reporting for customers and regulators.
The table below maps common SMB challenges to Concertium offerings and the practical benefits they provide.
This mapping shows practical paths for SMBs to adopt advanced detection without overwhelming internal teams and introduces concrete examples of SMB pain points and solutions.
What unique cybersecurity challenges do SMBs face that EDR addresses?
SMBs typically operate with small security teams, tight budgets, and a high relative impact from breaches, making rapid detection and containment essential.
Common issues include inconsistent patching, targeted phishing, and a lack of 24/7 monitoring that lets attackers operate unnoticed for longer periods.
EDR automates detection, supplies forensic evidence for fast triage, and enables policy-driven containment to prevent lateral spread.
For SMBs, these capabilities reduce breach impact and help meet contractual or regulatory obligations with managed support.
How does Concertium tailor EDR services to optimize cost and compliance for SMBs?
Concertium offers tiered MDR and Collective Coverage Suite (3CS) options that align capability with SMB budgets and compliance needs, blending AI-enhanced observability with managed analyst support to balance cost and protection.
Tiered plans let smaller clients start with core detection and containment and scale to advanced threat hunting or integrated compliance reporting as needs grow.
Our managed approach includes documented workflows and evidence collection to simplify audits and insurance requirements, helping SMBs demonstrate meaningful controls without building an internal SOC.
For SMBs seeking an approachable path to enterprise-grade defense, this model delivers predictable value and measurable outcomes.
With SMB needs covered, let’s review how real-time detection and automated response protect endpoints against urgent threats.
How Does Real-Time Threat Detection and Automated Response Protect Your Endpoints?
Real-time detection paired with automated response shortens attacker dwell time by isolating or remediating compromised endpoints based on high-confidence signals and pre-approved playbooks.
The flow starts with detection and risk scoring, triggers containment actions like network isolation or process termination, and continues with remediation and recovery to restore operations.
This automated pipeline stops ransomware spread, limits data exfiltration, and preserves forensic artifacts for post-incident analysis — all while analysts supervise and validate actions.
The numbered list below outlines a typical automated containment and remediation playbook, showing how automation supports speed and auditability.
- Detection and Scoring: Telemetry generates an alert that is scored and prioritized.
- Automated Containment: High-risk endpoints are isolated or offending processes terminated to prevent spread.
- Remediation and Recovery: Patching, file restoration, or rollback actions restore integrity and operations.
- Analyst Validation and Post-Incident Review: Analysts verify actions, adjust controls, and document findings.
What are the steps involved in automated threat containment and remediation?
Automated containment and remediation begins with detection, proceeds to immediate isolation of the affected endpoint, executes remediation steps such as artifact removal or system rollback, and concludes with validation and recovery tasks to restore normal operations.
Each automated step follows playbooks that define automation thresholds and analyst intervention points to ensure safety and avoid unnecessary disruption.
Recording and preserving forensic artifacts throughout the workflow keeps evidence intact for compliance and root-cause analysis.
This playbook-driven approach balances speed with control, reducing outage risk while enabling thorough follow-up.
How does automation reduce the impact of ransomware and zero-day exploits?
Automation reduces ransomware damage by executing containment actions — isolating infected hosts or blocking write privileges — within minutes, limiting file encryption and lateral movement.
Against zero-day exploits, behavioral detection plus automated isolation stops suspicious activity even before signatures exist, preventing attackers from scaling an exploit across the estate.
The result is lower mean time to recovery (MTTR), less data loss, and reduced operational cost after an incident.
These outcomes show why combining detection, AI-driven prioritization, and automated remediation is essential against time-sensitive threats.
When you’re ready to act, Concertium offers consultative assessments and managed MDR capabilities to bring these automated defenses into production and accelerate operational adoption of Advanced EDR.
Frequently Asked Questions
1. What types of organizations can benefit from Advanced EDR solutions?
Advanced EDR helps a wide range of organizations — from SMBs to large enterprises and regulated industries. SMBs often gain the most immediate lift because EDR paired with managed services delivers enterprise-grade security without needing a full in-house SOC. Larger organizations use EDR to strengthen existing defenses, speed incident response, and lower breach risk.
2. How does EDR support compliance requirements for businesses?
EDR supports compliance by capturing detailed telemetry and forensic records required for audits and regulatory reporting. It documents incidents, response actions, and system changes — useful for standards like GDPR, HIPAA, and PCI-DSS — and can automate parts of evidence collection and reporting to simplify audits.
3. What is the role of threat intelligence in Advanced EDR?
Threat intelligence enriches EDR by providing context on emerging threats, attack vectors, and known indicators. That context helps prioritize alerts and improves detection of sophisticated attacks that may bypass traditional defenses, enabling proactive response before incidents escalate.
4. How can organizations measure the effectiveness of their EDR solutions?
Measure EDR effectiveness with metrics such as mean time to detection (MTTD), mean time to response (MTTR), and the count of incidents detected and remediated. Also track reductions in dwell time, business impact, and operational downtime. Regular assessments, tabletop exercises, and analyst feedback further validate performance and highlight improvement areas.
5. What are the potential challenges in implementing Advanced EDR solutions?
Common challenges include integrating EDR with legacy security tools, finding skilled personnel to manage and interpret telemetry, and tuning systems to reduce false positives. Overcoming these requires clear policies, training, and — where appropriate — partnering with managed services to accelerate effective deployment.
6. How does AI enhance the capabilities of Advanced EDR?
AI improves EDR by enabling anomaly detection and behavioral analytics at scale. Machine learning models analyze large telemetry volumes to spot subtle deviations, prioritize high-risk alerts, and automate containment actions. This reduces alert fatigue, speeds response, and gives analysts richer context for investigations.
7. What should organizations consider when choosing an EDR vendor?
When selecting an EDR vendor, evaluate reputation, scalability, integration with existing tools, and the level of managed support available. Review features like automated response, threat intelligence integration, and reporting capabilities, and confirm the vendor’s commitment to ongoing updates as threats evolve.
Conclusion
Advanced Endpoint Detection and Response gives organizations the visibility and controls they need to detect threats faster, investigate with confidence, and respond automatically when seconds matter. By combining continuous telemetry with behavioral analytics and managed MDR services like Concertium’s, teams can reduce dwell time, lower operational risk, and meet compliance obligations. If you’re ready to strengthen your endpoint defenses, explore our EDR and managed services to find a path that fits your people, budget, and risk profile.