PCI DSS Compliance: Practical Requirements and Clear Guidance for Securing Payment Data
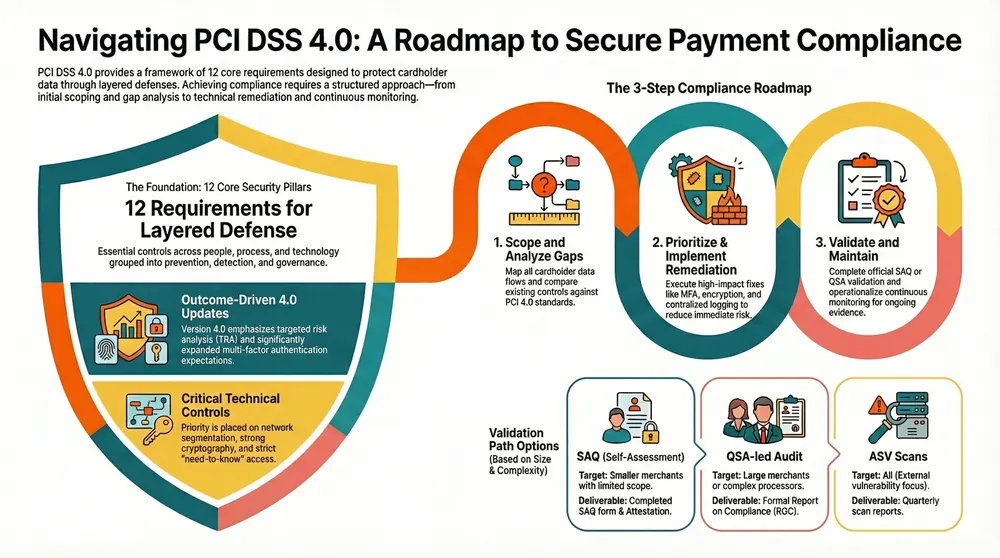
The Payment Card Industry Data Security Standard (PCI DSS) sets the minimum controls organizations must use to protect cardholder data and the Cardholder Data Environment (CDE). This guide explains PCI DSS in straightforward terms, summarizes the key changes in PCI DSS 4.0, and gives step-by-step actions teams can use to scope, fix, validate, and sustain compliance while keeping payment cards safe. You’ll get a clear run-through of the 12 core requirements, how v4.0’s targeted risk analysis and expanded MFA expectations change controls, and what auditors expect during SAQ or QSA validation.
We also map technical controls—encryption, segmentation, logging, and MFA—to concrete remediation steps, and explain how advisory and managed services speed the path to compliance. Finally, find practical roadmaps, gap-analysis templates, and an overview of how Concertium’s Compliance & Risk Advisory Services, Managed Cybersecurity Services, and AI-Enhanced Advanced Observability can support ongoing compliance.
What Are the PCI DSS Compliance Requirements and How Do They Protect Payment Card Data?
PCI DSS covers controls across people, process, and technology to stop unauthorized access, detect misuse, and enable rapid incident response. It applies to any organization that stores, processes, or transmits cardholder data and focuses on shrinking the attack surface inside the CDE through accurate scoping, segmentation, and evidence-backed controls. Mapping each requirement to practical technical controls helps teams prioritize remediation that produces measurable risk reduction. The section below lists the 12 high-level requirements in an actionable way so teams can spot immediate controls to implement and measure.
What Are the 12 Core PCI DSS Requirements Explained?
The 12 PCI DSS requirements group the essential activities for securing payment data and proving audit readiness—each one reduces a specific threat to the CDE.
- Install and maintain network security controls to prevent unauthorized access and isolate the CDE.
- Harden system configurations to remove default weaknesses and reduce exploitable settings.
- Protect stored cardholder data with strong cryptography and limit data retention where possible.
- Encrypt cardholder data when it’s transmitted across public or untrusted networks.
- Deploy and keep anti-malware tools updated to detect and block malicious code impacting payment systems.
- Develop and maintain secure systems and software, including tested change controls.
- Limit access to cardholder data strictly by business need-to-know to reduce insider risk.
- Identify and authenticate users and systems with strong credential controls and lifecycle management.
- Control physical access to areas containing cardholder data to prevent direct theft or tampering.
- Track and monitor all access to network resources and cardholder data using reliable logging.
- Regularly test security systems and processes with vulnerability scans and penetration testing.
- Maintain an information security policy and governance program to sustain controls and evidence.
Together these requirements form layered defenses—prevention, detection, and governance—so organizations both lower breach likelihood and can demonstrate due diligence to customers and regulators.
Introductory mapping table: the table below compares three representative PCI requirements with typical controls and the types of services that commonly support them.
That mapping shows how targeted technical controls meet requirement objectives and where advisory or managed services provide the expertise and operational capacity to implement them. The next section explains how PCI DSS 4.0 adjusts expectations for these controls.
How Does PCI DSS 4.0 Update Enhance Payment Security?
PCI DSS 4.0 puts more emphasis on outcome-driven controls and gives organizations room for documented, risk-based approaches via Targeted Risk Analysis (TRA). At the same time it tightens requirements around authentication, monitoring, and testing. Notable changes include broader MFA expectations for CDE access, stronger continuous monitoring and evidence collection requirements, and formal acceptance of custom control approaches when validated by a TRA. To prepare, prioritize MFA for privileged and remote access to the CDE, improve logging and retention, and adopt continuous detection to generate the audit-ready evidence assessors will expect. The next section outlines practical steps business owners can follow to achieve compliance efficiently.
How Can Business Owners Achieve PCI DSS Compliance Effectively?
Reaching PCI DSS compliance starts with accurate scoping and an evidence-driven remediation program aligned to business priorities and risk tolerance. A focused approach saves time and cost by isolating the CDE, removing unnecessary scope, and prioritizing high-impact controls such as MFA, encryption, and segmentation. Practical planning combines an initial gap analysis, a prioritized remediation backlog with clear owners and timelines, and validation planning (SAQ or QSA), followed by continuous monitoring. The roadmap below gives a concise sequence organizations can follow and explains how to operationalize each step or bring in external help to accelerate results.
- Scope and inventory: Identify every system, vendor, and dataflow that touches cardholder data.
- Gap analysis and risk prioritization: Compare existing controls to PCI DSS 4.0 and rank fixes by risk and effort.
- Implement remediations: Put segmentation, encryption, MFA, and centralized logging in place as priority fixes.
- Validate and document: Complete SAQ or QSA validation, gather evidence, and produce attestation.
- Maintain and monitor: Operate continuous monitoring, schedule periodic testing, and enforce governance to stay compliant.
This five-step roadmap turns compliance requirements into an executable program that supports initial validation and ongoing evidence collection. Teams needing assessment help can engage Concertium’s gap analysis and advisory services to map controls to requirements and produce a remediation roadmap; our Compliance & Risk Advisory Services can also assist with scoping and evidence collection.
The table below maps typical business profiles to recommended actions so leaders can pick the right path.
This guidance aligns organizational complexity with practical next steps and shows where managed or advisory services shorten time-to-compliance. The next sections cover common obstacles and a checklist you can use to move from assessment to validated compliance.
What Are the Common Challenges in Achieving PCI DSS Compliance?
Common pain points include inaccurate scoping of the CDE, legacy systems that are hard to remediate, and gathering audit-quality evidence. Limited resources and competing IT priorities can slow projects, while third-party integrations complicate responsibility and evidence collection. Documentation gaps—missing policies, incomplete change logs, or inconsistent baselines—often surface during assessments and require disciplined governance to fix. To address these issues, use phased remediation with clear owners, centralize logging to simplify evidence collection, and leverage advisory templates for scoping and policies to reduce rework during auditor preparation.
Those mitigation steps feed directly into a prioritized checklist teams can use to structure remediation and prepare for SAQ or QSA validation.
What Practical Steps Should Businesses Follow to Become PCI Compliant?
A concise, prioritized checklist speeds compliance and delivers measurable security improvements that lower breach risk and audit friction. Start with a short discovery sprint to map cardholder data flows and build a minimal-scoped CDE, then run a gap analysis that yields a prioritized remediation backlog. Apply quick wins first—enable MFA for remote and privileged access, enforce TLS for in-transit data, and introduce segmentation—to reduce scope and immediate risk. Medium-term work includes key management, tokenization or at-rest encryption, centralized logging with appropriate retention, and routine vulnerability scanning and penetration testing. Finally, assemble evidence packs for SAQ or QSA validation and operationalize continuous monitoring to keep controls effective over time.
This phased approach turns standards into projects with clear deliverables and sets the stage for how specialist providers can support execution.
What PCI DSS Certification Services Does Concertium Offer to Support Compliance?
Concertium combines advisory expertise, managed security operations, and advanced observability to support the full PCI DSS lifecycle. Our offerings—Compliance & Risk Advisory Services, Managed Cybersecurity Services, and AI-Enhanced Advanced Observability—align to different phases: advisory work scopes the CDE and produces remediation plans; managed services run and maintain controls; observability supplies continuous, audit-grade evidence. The subsections below explain how each service maps to specific PCI activities and what deliverables clients can expect.
How Do Compliance & Risk Advisory Services Facilitate PCI DSS Compliance?
Our Compliance & Risk Advisory Services typically start with scoping the CDE and a detailed gap analysis against PCI DSS 4.0, producing a prioritized remediation roadmap and an evidence catalog. Deliverables often include a formal gap report, a remediation project plan with owners and timelines, policy templates mapped to requirements, and hands-on support for evidence collection during validation. Advisory work shortens time-to-compliance by clarifying mandatory controls versus areas suitable for an alternative approach or TRA, and by preparing teams for auditor questions. Ongoing advisory check-ins help ensure controls remain effective after validation.
This advisory foundation pairs with managed detection and observability to keep controls operating and evidence flowing, which the next subsection describes.
How Do Managed Cybersecurity and AI-Enhanced Observability Services Support Payment Security?
Managed Cybersecurity Services operationalize key controls—centralized logging, SIEM, endpoint protection, vulnerability management, and incident response—so evidence is continuously captured and controls stay effective. AI-Enhanced Advanced Observability adds analytics to logs and telemetry to improve detection and streamline forensics, producing alerts, dashboards, and incident timelines that simplify auditor requests for proof of monitoring and testing. Practical outputs include real-time alerts for suspicious CDE access, automated anomaly detection across payment flows, and exportable evidence bundles for validation. Combined, managed services and observability make compliance an ongoing operational posture rather than a one-time checkbox.
These service suites close the loop between strategic planning, control implementation, and audit-ready evidence. The next section explores the technical controls that protect cardholder data.
How Does Protecting Cardholder Data Ensure Payment Security and Compliance?
Protecting cardholder data depends on strong cryptography, effective network segmentation, strict access controls, and comprehensive logging to reduce exposure and enable fast detection and response. Encryption secures data at rest and in transit, segmentation narrows the CDE and reduces lateral movement, and role-based access with strong authentication prevents credential misuse. Logging and continuous monitoring provide the forensic trail auditors expect and support incident response, while regular testing verifies that controls remain effective. The following subsections cover encryption and network expectations and the updated MFA requirements central to PCI DSS 4.0.
What Encryption and Network Security Measures Are Required for PCI DSS?
PCI DSS requires strong cryptography for stored and transmitted cardholder data, approved TLS configurations for in-transit protection, and sound key management to prevent unauthorized decryption. Best practices include using current TLS versions and cipher suites, encrypting backups and databases that contain cardholder data, and applying hardware or software key management with rotation and restricted access. Network segmentation—via firewalls, VLANs, and access control lists—should isolate the CDE to limit lateral movement and shrink audit scope. Common pitfalls include weak ciphers, unencrypted backups, and unmanaged key access; fixing these issues prevents many exposures and simplifies validation.
These cryptographic and network controls work hand-in-hand with authentication and access controls to form layered protection for the CDE.
Why Is Multi-Factor Authentication Essential for Cardholder Data Environment Access?
Multi-Factor Authentication (MFA) is now a core requirement for CDE access because it greatly reduces the risk of credential compromise—the most common vector in payment breaches. Under PCI DSS 4.0, MFA is required for all access into the CDE, covering privileged and non-privileged users as well as remote connections. Acceptable approaches combine knowledge, possession, and inherence factors without single points of failure. Practical deployments include hardware tokens, mobile authenticators with device posture checks, and adaptive MFA integrated with SSO and privileged session controls. Avoid weak implementations such as SMS-only verification, unprotected authentication logs, or missing MFA for service accounts—these gaps are frequently flagged in audits and breach investigations.
When paired with segmentation and encryption, robust MFA reduces both the chance and impact of a compromise in the CDE.
What Is the PCI DSS Audit and Validation Process for Maintaining Compliance?
PCI DSS validation follows two main paths—Self-Assessment Questionnaire (SAQ) for smaller scoped merchants and QSA-led audits for larger or higher-risk environments—each with differing evidence expectations and timelines. Validation requires clear scoping, evidence collection (configurations, logs, policies), testing (vulnerability scans and penetration tests), and either SAQ submission or a formal QSA Report on Compliance and Attestation. Ongoing maintenance means periodic revalidation, continuous monitoring, and timely remediation of new findings. The table below compares SAQ and QSA validation paths so teams can pick the right route and plan deliverables.
This comparison highlights cost-versus-risk trade-offs and helps plan audit windows and evidence collection. The following sections describe how risk assessments are run and the roles QSAs and SAQs play in validation.
How Are Risk Assessments and Gap Analyses Conducted for PCI DSS?
Risk assessments and gap analyses start with discovery of systems and dataflows, then map existing controls to PCI DSS to find gaps and estimate exposure. Typical methods include asset inventory, threat and risk scoring, configuration review, and evidence sampling; teams use automated scanners, configuration management databases, and interviews to validate processes. Deliverables include a scored gap report, a prioritized remediation list, and recommended compensating controls where immediate fixes aren’t practical. These artifacts drive remediation governance and provide a defensible basis for alternative approaches validated through a Targeted Risk Analysis.
Clear, prioritized gap findings speed remediation and create the documentation auditors expect during validation.
What Roles Do Qualified Security Assessors and Self-Assessment Questionnaires Play?
Qualified Security Assessors (QSAs) perform independent validation and produce a formal Report on Compliance for complex or high-risk organizations, while Self-Assessment Questionnaires (SAQs) let smaller entities attest compliance against the relevant subset of requirements. Preparing for a QSA engagement typically requires comprehensive evidence packs, remediation logs, and access to system owners, plus deeper technical testing and interviews during the audit. SAQ preparation focuses on completing the correct SAQ type (for example, SAQ A or SAQ D), documenting controls, and collating supporting artifacts. Both paths demand careful evidence organization; choosing early between SAQ and QSA improves planning and avoids last-minute remediation delays.
Selecting the right validation path early reduces surprises and speeds attestation.
What Are the Business Benefits and Risks Associated with PCI DSS Compliance?
PCI DSS compliance brings clear business benefits—lower breach likelihood, stronger operational controls, and greater customer trust that can translate into competitive advantage—while non-compliance risks fines, remediation costs, and reputational harm. Demonstrating compliance reassures partners and customers that cardholder data is handled with discipline and can influence contract terms and merchant standing. Conversely, failure to comply can lead to fines, higher transaction fees, mandatory forensic work, and even loss of payment-processing privileges. The subsections below explore how compliance builds trust and the financial consequences of control failures.
How Does Compliance Enhance Customer Trust and Competitive Advantage?
Maintaining PCI DSS compliance shows customers, partners, and payment processors that you take payment security seriously and have formal controls in place. Compliance is a powerful trust signal in sales and procurement—attestations, policy evidence, and audit reports differentiate organizations during vendor reviews. Practical trust signals include transparent compliance statements, clear incident response commitments, and published proof points around monitoring and testing cadence. For many buyers, documented compliance lowers perceived third-party risk and can shorten procurement cycles or unlock relationships that require robust payment security.
Those commercial benefits often justify the investment in compliance programs and can offset operational costs through new opportunities and lower risk premiums.
What Financial Penalties and Security Risks Result from Non-Compliance?
Non-compliance can trigger fines from card brands and acquiring banks, mandatory forensics, remediation expenses, and potential increases in transaction fees or loss of merchant status—costs that often exceed proactive program spending. Beyond fines, a breach brings remediation bills, incident response and legal costs, and long-term revenue loss from damaged trust. Even moderate breaches can produce six-figure recovery costs when fines, forensics, and customer restitution are included. Prioritizing controls and working with advisory or managed providers reduces exposure and speeds recovery if an incident occurs.
To capture these safeguards and benefits, many organizations start with a Concertium gap analysis or vulnerability scan to get a rapid, evidence-based view and a clear next step toward validated compliance.
Frequently Asked Questions
What is the difference between Self-Assessment Questionnaires (SAQ) and Qualified Security Assessors (QSA)?
SAQs let smaller merchants self-evaluate against the relevant PCI DSS requirements and submit an attestation of compliance. QSAs are independent experts who perform formal audits and produce a Report on Compliance for larger or higher-risk entities. Choose SAQ or QSA based on transaction volume, how card data is handled, and acquiring-bank requirements—QSAs deliver deeper technical validation, while SAQs are suitable for simpler, lower-risk flows.
How often should organizations conduct vulnerability scans and penetration tests for PCI DSS compliance?
PCI DSS requires external vulnerability scans at least quarterly and after significant network changes. Penetration tests should be performed at least annually or after major infrastructure changes. Regular scanning and testing help identify weaknesses before attackers find them and provide required evidence for validation.
What are the consequences of failing to achieve PCI DSS compliance?
Failing to comply can lead to substantial fines, increased transaction fees, mandatory forensic investigations, and potential suspension of payment processing privileges. The financial and reputational fallout from a breach—remediation, legal exposure, and lost customers—can far exceed the cost of a proactive compliance program.
How can organizations ensure ongoing PCI DSS compliance after initial certification?
Ongoing compliance requires continuous monitoring, routine audits, and current documentation of policies and procedures. Establish governance with periodic risk assessments, scheduled vulnerability scans, and regular penetration testing. Stay current with PCI DSS updates and adjust controls accordingly. Many organizations retain advisory or managed services to sustain evidence collection and reduce operational burden.
What role does employee training play in achieving PCI DSS compliance?
Employee training is essential—human error is a frequent cause of data incidents. Regular training should cover secure data handling, phishing awareness, strong password and MFA practices, and incident reporting. Building a security-aware culture reduces compliance gaps and strengthens overall defenses.
What are the best practices for managing third-party vendors in relation to PCI DSS compliance?
Manage vendors through thorough due diligence, clear contractual security requirements, and ongoing assessments. Verify vendors’ compliance posture, require appropriate evidence, and define responsibility boundaries for cardholder data. Regular audits or evidence requests and open communication help address issues quickly and reduce third-party risk.
Conclusion
PCI DSS compliance protects cardholder data and strengthens operational trust. By implementing the 12 core requirements and using expert advisory and managed services, organizations can reduce breach risk and the costs that follow. Taking a pragmatic, prioritized approach demonstrates a business-wide commitment to security and can be a differentiator in the market. Start your path to stronger payment security with a targeted assessment—explore our tailored compliance solutions to take the next step.