XDR Security Solutions: Comprehensive Extended Detection and Response Platforms for Business Protection
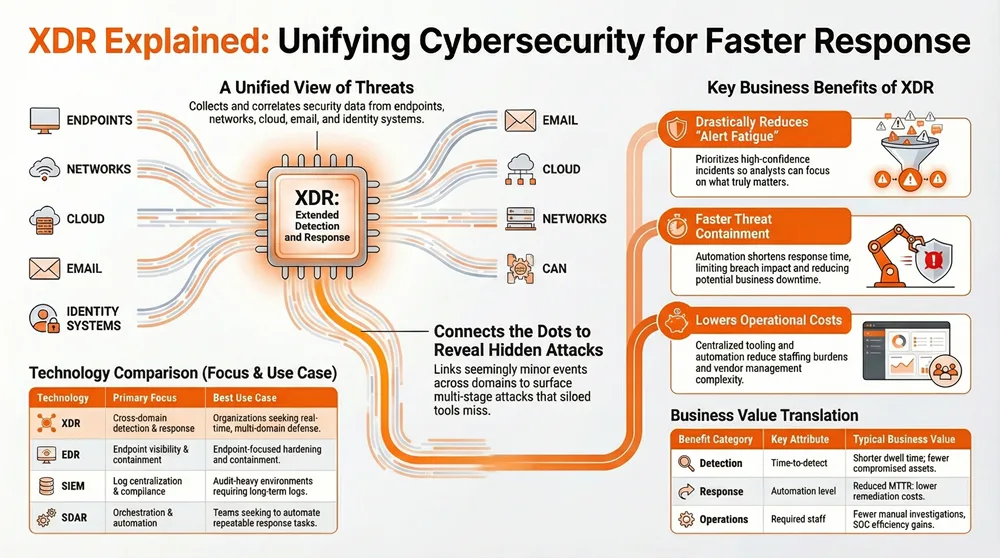
Extended Detection and Response (XDR) is a unified cybersecurity approach that collects and correlates telemetry across endpoints, networks, cloud, email, and identity systems to detect, investigate, and respond to complex, multi-stage attacks. This article explains how XDR platforms work, why they matter for businesses facing alert fatigue and sophisticated adversaries, and how organizations can evaluate and implement XDR to reduce dwell time and improve incident outcomes.
Readers will learn the core components of XDR, measurable benefits and KPIs to track, comparisons with EDR, SIEM, and SOAR, and a practical implementation roadmap tailored for business owners. The article also describes how managed XDR services operationalize these capabilities and where a provider-led, AI-enhanced observability stack can accelerate time-to-value. Finally, we will outline challenges and mitigations, vendor-selection guidance, and reasons to consider a managed, unified security operations approach for sustained protection.
What is Extended Detection and Response and Why Does It Matter?
Extended Detection and Response (XDR) is a security paradigm that extends traditional endpoint detection and response by ingesting telemetry from multiple domains and applying correlation and automation to detect complex threats faster. XDR works by normalizing diverse data streams, enriching events with context, and applying analytics and orchestration to surface high-confidence incidents that reduce false positives and shorten time-to-detect. The result is improved situational awareness and faster containment across the attack surface, which directly reduces breach impact and operational overhead. Understanding XDR’s role begins with its core capabilities and the practical problems it addresses.
To ground the concept in practice, some providers package multi-domain telemetry, analytics, and managed operations into bundled suites that deliver integrated XDR outcomes for customers. Concertium, for example, frames XDR capabilities through a unified suite that combines observability, managed detection, and incident management to deliver end-to-end protection. This provider-led packaging is designed to bridge the technical promise of XDR with operational realities, particularly for organizations that need 24×7 coverage and streamlined vendor management. The following subsections explain how XDR enhances cross-domain detection and outline the platform components that enable those outcomes.
How Does XDR Enhance Cross-Domain Threat Detection?
XDR enhances cross-domain threat detection by ingesting telemetry from endpoints, network flows, cloud logs, email gateways, and identity systems, then correlating those signals through analytics engines to reveal multi-stage attack chains. The mechanism involves data normalization, enrichment with threat intelligence, and behavioral baselining so anomalies across domains can be stitched into coherent incidents rather than siloed alerts. By linking seemingly minor events — a suspicious email click, anomalous cloud API usage, and lateral movement on endpoints — XDR surfaces patterns that single-domain tools often miss. This cross-domain correlation reduces false positives, accelerates prioritization, and enables earlier containment, improving measurable KPIs like time-to-detect and mean time to respond.
Research further supports the effectiveness of XDR’s multi-domain approach, particularly when leveraging machine learning for advanced threat detection.
XDR & EDR Performance: ML for Cyber Threat Detection
These results demonstrate that incorporating cross-domain telemetry with XDR substantially improves detection coverage, particularly for gradient-boosted models, and underscore the growing importance of XDR for effective, proactive cyber defense.
Evaluating ML Performance in EDR and XDR Systems Against Common Cyber Threats, 2025
This cross-domain view also supports threat-hunting and hypothesis-driven investigations because analysts can pivot across artifacts with contextual links, reducing investigation cycle time. The next section explains the core technical components that make this cross-domain visibility possible and how XDR has evolved from earlier security models.
What Are the Core Components and Evolution of XDR Platforms?
Modern XDR platforms are built from three core components: telemetry collection and normalization, analytics and correlation (often AI/ML-powered), and automated response and orchestration. Telemetry collection pulls structured logs and rich contextual data from endpoints, network sensors, cloud services, email, and identity providers. Analytics engines then apply rule-based logic, statistical anomaly detection, and machine learning to correlate events into prioritized incidents. Finally, automation and orchestration enable containment actions, playbook execution, and handoffs to human analysts or managed responders.
The evolution from EDR and SIEM-centric approaches shows a progression from siloed telemetry and retrospective logging to real-time, context-rich correlation and operational automation. Early EDR focused on endpoint telemetry, SIEM centralized logs for compliance and analysis, and XDR converges these streams with native response capabilities. This evolution is important because it signals a shift from alert overload to outcome-driven detection and response, which is particularly valuable when combined with continuous observability and managed operations.
Indeed, the fundamental goal of XDR has always been to unify disparate security tools into a cohesive system for enhanced threat visibility.
XDR Integration: Unifying Disparate Security Tools
It examines how XDR solutions integrate multiple security products for a cohesive system, enhancing overall security postures. The initial objective of XDR was to integrate these disparate security tools to provide a unified view of threats.
Integrating AI/ML in cybersecurity: An analysis of open XDR technology and its application in intrusion detection and system log management, K Demertzis, 2024
What Are the Key Benefits of XDR Security for Businesses?
XDR delivers measurable business benefits by improving detection speed, reducing mean time to respond (MTTR), streamlining security operations, and supporting compliance objectives. At the operational level, XDR reduces alert fatigue through prioritized, context-rich incidents and automates routine containment steps to reduce manual toil. At the business level, reduced dwell time decreases potential financial and reputational impact from breaches, while unified visibility reduces tool sprawl and vendor management overhead. The table below compares primary benefit categories, attributes to track, and typical business values organizations can expect from a mature XDR deployment.
This perspective is reinforced by external research highlighting the operational advantages of managed XDR services.
MXDR: Reducing Alert Fatigue & Accelerating Threat Response
A key benefit of MXDR is its ability to reduce “alert fatigue” by using automation and analysts to triage the flood of alerts from various security tools. It also accelerates threat detection and response by correlating telemetry data across the infrastructure to identify risks in real-time.
Extending detection and response: how MXDR evolves cybersecurity, AS George, 2023
Different benefit categories map to operational attributes and measurable outcomes that business leaders can track.
This mapping shows how detection and response improvements translate into operational savings and reduced business risk, making it easier to justify XDR investments. Below are direct ways those improvements manifest in day-to-day security operations.
XDR’s practical benefits also appear in concrete KPIs and outcomes:
- Faster Detection: Correlated signals reduce mean time to detect by consolidating alerts into actionable incidents.
- Reduced Downtime: Automated containment can limit spread and reduce operational disruption.
- Lower Operational Costs: Centralized tooling and managed services reduce staffing burdens and tool licensing complexity.
These benefits create a compelling value proposition for organizations seeking to modernize their security operations while controlling costs and complexity.
How Does XDR Improve Threat Detection and Incident Response?
XDR improves threat detection and incident response by combining correlated telemetry, AI-driven prioritization, and automated playbooks that trigger containment actions without waiting for manual intervention. Correlation reduces false positives because multiple corroborating signals are required to escalate an incident, which increases analyst confidence and allows focus on high-risk events. Automated response routines — such as isolating an endpoint, revoking credentials, or blocking malicious IPs — shorten MTTR while human analysts handle complex decisions. The integrated workflow also supports human-in-the-loop operations where analysts validate AI-suggested actions before full automation, preserving control while increasing speed.
Consider a hypothetical ROI scenario: a mid-sized company that reduces average containment time from 12 hours to 2 hours may avoid extended production outages and limit data exposure, which can equate to significant financial savings per incident. The next subsection explains how XDR optimizes ongoing SOC operations and compliance reporting.
In What Ways Does XDR Optimize Security Operations and Compliance?
XDR optimizes SRM and SOC workflows by reducing alert volume, enriching alerts with context, and providing centralized dashboards for triage and case management. Contextual enrichment (process lineage, user identity, recent cloud activity) accelerates investigations and reduces time spent pivoting between tools. For compliance, XDR streamlines evidence collection by preserving correlated incident artifacts and generating structured reports aligned with audit frameworks. Recommended metrics to track include false positive rate, analyst time per investigation, MTTR, and number of automated playbook executions.
These operational improvements lead to predictable improvements in SOC throughput and audit readiness, and they create a repeatable mechanism for demonstrating controls to stakeholders. The next section describes how a managed XDR approach packages these capabilities into operational services for customers.
How Does Concertium Deliver Managed XDR Services Through Its Collective Coverage Suite?
Concertium delivers managed XDR outcomes through its Collective Coverage Suite (3CS), which bundles AI-Enhanced Advanced Observability, Managed Detection & Response (MDR), and Post-Breach Services into a cohesive offering designed to provide end-to-end protection. The suite aligns telemetry collection, 24x7x365 monitoring, and incident response playbooks so organizations gain unified security operations without assembling disparate point products. Concertium’s positioning emphasizes proactive threat mitigation using AI-driven observability plus continuous MDR to reduce dwell time and coordinate post-breach containment and recovery. This managed approach is aimed at educating on cybersecurity, showcasing services, generating leads, and supporting clients through full incident lifecycles.
For organizations evaluating provider-led XDR, Concertium’s suite focuses on outcomes such as faster detection, reduced recovery time, and simplified vendor management through a single operational model. Service highlights include continuous observability that feeds detection analytics, a staffed MDR function for 24/7 monitoring and hunting, and post-breach services to manage containment and remediation. Prospective customers are encouraged to request a consultation or vulnerability scan to assess readiness and expected improvements in detection and response.
What Role Does Managed Detection and Response Play in XDR?
Managed Detection and Response (MDR) operationalizes XDR by providing expert analysts who monitor correlated incidents, pursue proactive threat hunting, and coordinate response actions with customers. MDR responsibilities include continuous alert validation, escalation of confirmed incidents, threat-hunting campaigns to uncover latent compromises, and collaboration with internal teams for containment. For many SMBs, MDR supplies the SOC expertise and staffing they lack, transforming XDR telemetry into real-world defense outcomes and reducing the burden on in-house IT staff.
This managed capability is particularly valuable when integrated with automated playbooks because it combines human judgment with deterministic response steps, ensuring both speed and correctness during incidents. The following list summarizes typical MDR responsibilities that support XDR outcomes:
- 24×7 monitoring and alert validation to maintain continuous coverage.
- Proactive threat hunting to identify stealthy or emerging threats.
- Coordinated incident response with documented SOPs and escalation paths.
- Forensic evidence collection and handover to internal teams or external counsel when needed.
These MDR activities reduce time-to-detect and mean time to remediate while allowing internal teams to focus on business priorities rather than constant alert triage.
How Does AI-Enhanced Advanced Observability Power XDR Insights?
AI-Enhanced Advanced Observability powers XDR by aggregating telemetry in real time and applying machine learning to detect anomalies, assign risk scores, and prioritize alerts for analysts. Observability outputs include anomaly scores, enriched event context, and prioritized incident queues that feed correlation engines, enabling faster and more accurate decision-making. AI models can surface subtle deviations in user behavior, cloud API usage, or process activity that rule-based systems might miss, and they help reduce noise by ranking alerts on likely impact.
By providing enriched, prioritized inputs to the XDR correlation layer, observability reduces investigative overhead and improves the signal-to-noise ratio for analysts, which accelerates containment and reduces false positives. The next section turns to comparisons between XDR and other security technologies to clarify how XDR fits into broader security architectures.
How Does XDR Compare to EDR, SIEM, and SOAR Security Solutions?
XDR, EDR, SIEM, and SOAR address different layers of security operations with overlapping capabilities; understanding their strengths and limitations helps organizations design complementary architectures. In short, EDR focuses on endpoint detection and containment, SIEM centralizes logs and supports compliance and forensic searches, SOAR automates playbooks and orchestration, while XDR aims to unify multi-domain telemetry with built-in correlation and response. The table below summarizes each technology’s primary focus, strengths, limitations, and best-fit use cases.
To support quick comparisons, the following table presents a concise side-by-side view useful for decision-makers.
This comparison shows that XDR complements rather than simply replaces existing technologies in many deployments, and hybrid approaches often deliver the best balance between detection fidelity and compliance obligations. Below are concise contrasts that address common decision points.
What Are the Differences Between XDR and Endpoint Detection and Response?
XDR differs from traditional Endpoint Detection and Response (EDR) primarily in scope and data sources: EDR concentrates on endpoint telemetry and endpoint containment, while XDR aggregates endpoint data alongside network, cloud, email, and identity telemetry for cross-domain correlation. Where EDR may isolate a compromised device, XDR can coordinate containment across related assets and revoke credentials or block network paths as part of a broader response. For SMBs, EDR remains essential for endpoint hardening, but XDR adds value by reducing blind spots and improving detection of multi-stage attacks that pivot across environments.
This multi-domain capability makes XDR particularly effective for detecting attack chains that begin with social engineering and escalate to lateral movement, which a pure EDR deployment might not fully detect. The next subsection explains how XDR interacts with SIEM and SOAR.
Does XDR Replace SIEM and SOAR or Complement Them?
XDR typically complements SIEM and SOAR rather than outright replacing them in many enterprise environments. SIEM remains valuable for long-term log retention, compliance reporting, and complex forensic searches, while XDR focuses on real-time correlation and response; SOAR provides the orchestration layer that automates complex, cross-tool workflows. Decision guidelines include retaining SIEM when long-term logs and regulatory reporting are required, adopting XDR for real-time detection and automated containment, and using SOAR to codify and automate repeatable response processes that span multiple tools.
When integrated, these technologies create a layered architecture where SIEM stores historical telemetry, XDR rapidly identifies and responds to incidents, and SOAR executes complex playbooks that require coordination. This hybrid approach leverages the strengths of each technology to deliver both compliance and rapid defense.
What Are the Challenges and Best Practices for Implementing XDR Security?
Implementing XDR introduces practical challenges such as integration complexity, data normalization, change management, and cost considerations, but there are established mitigations and best practices to manage these issues. Common obstacles include connector gaps, inconsistent telemetry quality, and workflow changes for SOC teams adapting to new consolidated alerts. Effective mitigations involve phased rollouts, standardizing connectors and data schemas, leveraging managed services to address skill gaps, and defining clear success metrics and SLAs. The table below maps frequent implementation challenges to practical mitigations and best practices.
The following table links implementation challenges to provider-led mitigations that organizations can apply.
Addressing these challenges with a measured plan reduces deployment risk and accelerates time-to-value. Below are actionable tactics to overcome common integration hurdles.
How Can Businesses Overcome Integration and Complexity Issues in XDR Deployment?
Businesses can overcome integration and complexity issues by adopting a phased implementation, prioritizing high-value data sources, and using standardized connector libraries and APIs to ensure consistent telemetry ingestion. Starting with endpoints, cloud workloads, and identity logs provides a strong detection foundation; subsequent phases can add email telemetry and network flows. Managed services can fill operational gaps while internal teams adapt processes, and clear KPIs (MTTR, false positive rate, analyst time) should be tracked to measure progress. Regular cadence reviews and incremental automation reduce disruption and refine playbooks over time.
These practical steps combine technical and organizational measures to ensure XDR deployments deliver predictable improvements and align with business risk tolerance. The next subsection provides an ordered checklist for business owners planning an XDR rollout.
What Steps Should Business Owners Follow for Successful XDR Implementation?
Business owners should follow a step-by-step plan: assess current telemetry and readiness, define success metrics and SLAs, run a targeted pilot, refine detection playbooks based on pilot outcomes, and proceed to staged enterprise-wide deployment. The pilot phase should validate connectors, tune analytics to minimize false positives, and test automated containment in controlled conditions. Stakeholders to involve include IT, security, legal, and business owners so response actions align with operational constraints. A timeline of 3–6 months for pilot and initial rollout is typical for many organizations, with continuous improvement cycles thereafter.
Below is a practical checklist to guide implementation:
- Assess telemetry coverage: Inventory endpoints, cloud services, email, and identity sources.
- Define metrics and SLAs: Establish MTTR targets and acceptable false positive thresholds.
- Run a pilot: Validate connectors, tune correlation rules, and test playbooks.
- Scale in phases: Add telemetry sources and automation iteratively while measuring KPIs.
This ordered approach ensures measurable outcomes and reduces deployment risk by validating assumptions before full-scale adoption.
Why Choose Concertium for Your XDR Security Needs?
Concertium positions its Collective Coverage Suite (3CS) to deliver unified security operations that emphasize end-to-end protection, proactive threat mitigation, and comprehensive breach management. The suite combines AI-Enhanced Advanced Observability with 24x7x365 Managed Detection & Response and targeted Post-Breach Services to reduce recovery time and improve visibility across the environment. Concertium’s messaging stresses a unified operations model that simplifies vendor management and provides managed expertise to organizations needing continuous coverage. For organizations that prefer a provider-led path to XDR, Concertium offers consultative assessments and services designed to demonstrate measurable detection and response improvements.
How Does Concertium’s Experience and Unified Security Operations Benefit Businesses?
Concertium’s unified security operations reduce complexity by consolidating observability, detection, and response under a single operational model, which reduces vendor sprawl and simplifies incident coordination. This operational maturity helps customers expect faster response times, consistent playbook execution, and clearer accountability during incidents. Centralized incident coordination also reduces the need for customers to manage multiple vendor handoffs, and the managed model supports smaller teams that lack full SOC staffing. These outcomes make it easier for business leaders to measure improvements against KPIs such as MTTR and analyst productivity.
Unified operations plus managed expertise deliver predictable incident handling and allow in-house teams to focus on strategic initiatives rather than daily alert triage. The next subsection outlines representative client outcomes that illustrate these effectiveness claims.
What Client Success Stories Demonstrate Concertium’s XDR Effectiveness?
Representative client vignettes highlight measurable outcomes such as substantial improvements in time-to-detect, reduced containment times, and simplified post-breach coordination — outcomes that mirror the core benefits of a managed XDR approach. For example, anonymized engagements show organizations achieving faster detection through consolidated telemetry and reducing mean time to remediate via automated containment and managed response. These vignettes demonstrate industry-relevant improvements for SMBs and mid-market customers that require practical, cost-effective security outcomes. Readers seeking deeper proof points are encouraged to request case studies or references to understand industry-specific results.
These success stories illustrate the practical value of combining AI-enhanced observability with continuous MDR and focused post-breach services, and they provide decision-makers with tangible expectations for similar deployments.