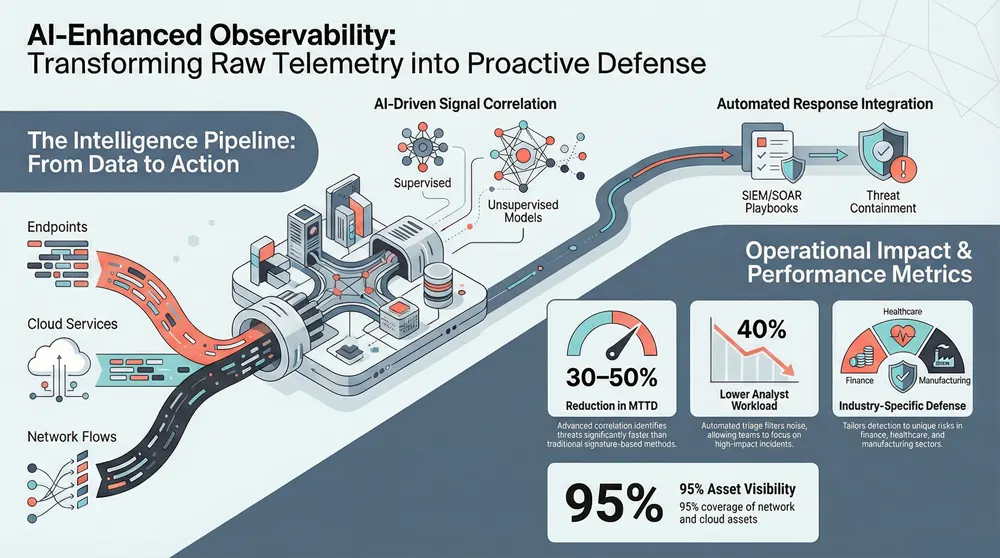
AI-enhanced observability brings together broad telemetry and machine learning to give security teams continuous, contextual insight — reducing blind spots and speeding threat detection. This article shows how multi-layer telemetry is collected, how analytic models surface high-fidelity alerts, and how signals are turned into prioritized, actionable outcomes for SOC and risk teams. Many organizations today suffer from fragmented visibility across endpoints, cloud services, and network flows, which lengthens dwell time and raises response costs.
We explain systematic approaches that convert raw data into intelligence you can act on. You’ll get a clear view of core observability components, the ML techniques that enable proactive detection, the operational gains for network monitoring, and the compliance and industry-specific defenses observability supports. Where relevant, we show how SIEM, UEBA, XDR and threat intelligence interoperate with modern AI to improve detection accuracy, guide remediation, and help keep your business running.
What is AI-Enhanced Advanced Observability in Cybersecurity?
AI-enhanced observability is a continuous intelligence layer built from wide telemetry collection, resilient data pipelines, and machine learning that correlates disparate signals into prioritized security insight. It ingests network flows, endpoint telemetry, cloud logs and user activity, then uses feature engineering and AI models to spot anomalous patterns that suggest compromise or misconfiguration. The practical benefit is earlier, better-contextualized detection that shortens investigations and cuts false positives — improving security operations efficiency and overall risk posture. Framing these building blocks makes it clear why observability goes beyond monitoring: it’s an always-on layer that supports detection, response and compliance.
AI boosts observability through scalable correlation and adaptive baselining. The table below defines the primary components and their roles so implementation planning is concrete and actionable.
This mapping clarifies how each element raises detection fidelity and shapes operational outcomes — useful when designing architecture or comparing vendors.
How does AI improve deep cybersecurity observability?
AI deepens observability by spotting subtle deviations across high-dimensional telemetry, correlating signals at scale and surfacing indicators human analysts might miss. At its core are pattern recognition and adaptive baselining: unsupervised models learn normal behavior for users and devices, while supervised classifiers detect known malicious signatures enhanced with threat intelligence. The outcome is prioritized alerts with rich contextual metadata that point to likely root causes and affected assets — cutting noise and focusing analyst time on high-impact incidents. Those insights also speed threat hunting by suggesting relevant query vectors and correlated artifacts.
With detection improvements understood, the next section covers the architecture and components needed to turn AI-driven observability into operational reality.
What are the core components of AI-driven observability solutions?
Key components are telemetry ingestion, feature stores, modeling layers, analyst-facing dashboards, and integrations with SIEM/SOAR for response automation. Ingestion pulls network flows, endpoint telemetry, cloud events and app logs; feature stores persist engineered attributes for consistent, real-time scoring. Modeling layers host supervised and unsupervised algorithms plus graph analytics for lateral-movement detection, while dashboards translate model outputs into analyst-ready insights. SIEM and SOAR integrations ensure alerts trigger automated playbooks and evidence collection for post-breach investigations, closing the loop from detection to response.
The compact table below pairs technologies with their function and business impact for quick reference.
Together, these components turn telemetry into prioritized, actionable intelligence that lets organizations scale AI-driven detection.
Next, we explore how AI changes detection paradigms and the ML techniques that enable proactive security.
How Does AI-Driven Threat Detection Transform Cybersecurity?
AI-driven detection moves security operations from reactive firefighting to proactive, predictive defense. Instead of relying only on signatures, teams can use behavioral analytics, temporal correlation and probabilistic risk scoring to surface anomalous sequences and early indicators. That shift delivers measurable results: faster mean time to detect (MTTD), lower mean time to respond (MTTR), and fewer false positives — so SOCs can concentrate on real threats. Practically, this creates new analyst workflows that depend on model-provided context and tighter links between detection engines, threat intelligence and orchestration tools.
Here are the core mechanisms that illustrate AI’s transformative effect.
- Anomaly Detection: Spots deviations from learned baselines to catch unknown threats.
- Predictive Analytics: Correlates early indicators to forecast likely attack paths.
- Behavioral Correlation: Joins user and entity signals to trace lateral movement.
These mechanisms inform model selection and deployment patterns. Many providers operationalize them by feeding model outputs into SIEM/XDR workflows and automated playbooks.
Concertium applies these principles in its AI-Enhanced Advanced Observability service, combining ML-driven anomaly detection with SIEM enrichment to deliver prioritized alerts and evidence collection. That implementation shows how observability models can feed orchestration layers to speed containment while preserving context for compliance.
What machine learning techniques enable proactive threat detection?
Proactive detection relies on a mix of ML approaches: supervised classifiers for known signatures, unsupervised models for novel anomaly detection, semi-supervised methods for environments with limited labels, and graph analytics to expose lateral movement and attack chains. Supervised models give high precision when labeled data exist; unsupervised models reveal new patterns without labels; semi-supervised approaches blend both advantages as environments evolve. Graph analytics stitches entities and events into attack paths, uncovering complex multi-stage intrusions that simple rule-based systems miss.
Each technique has trade-offs in data needs, false-positive behavior and maintenance. Effective observability platforms layer multiple approaches to balance coverage, precision and operational overhead — helping architects choose models that match detection goals and constraints.
How does predictive AI security anticipate emerging cyber threats?
Predictive AI uses trend analysis, time-series forecasting and ensemble models to surface precursors — reconnaissance spikes, credential-stuffing campaigns, or exploit scanning — before compromise. Enriching telemetry with threat intelligence and vulnerability context lets models score exploitation likelihood and prioritize at-risk assets for preemptive hardening or focused monitoring. The result: early-warning dashboards and prioritized mitigation plans that shrink exploit windows and guide targeted patching or segmentation.
This anticipatory view is particularly valuable when teams face patch backlogs or limited remediation resources: predictive scores help focus effort where exploitability and impact intersect.
What Are the Benefits of AI Network Monitoring for Businesses?
AI network monitoring gives businesses clearer visibility across hybrid environments, automated detection of anomalous traffic, and operational efficiencies that lower security costs and downtime. By correlating endpoint, cloud and network telemetry, AI-driven monitoring removes blind spots and surfaces risky lateral movement, misconfigurations and data-exfiltration attempts earlier. The business outcomes include shorter MTTR, fewer false positives and better uptime — measurable gains that reduce financial and reputational risk. For security teams, AI cuts analyst fatigue by automating triage and surfacing context-rich, prioritized incidents so responders act with confidence and speed.
Below are the primary business benefits and the common measurements organizations use to track them.
AI network monitoring delivers measurable improvements:
- Reduced MTTR: Faster detection and contextual evidence shorten containment and remediation windows.
- Fewer Blind Spots: Cross-layer telemetry uncovers unknown assets and ephemeral cloud instances.
- Operational Efficiency: Automated triage and playbooks lower analyst time per incident.
- Improved Detection Accuracy: Model-based scoring reduces false positives and raises signal-to-noise.
These outcomes directly affect security economics and help justify investment in observability platforms. The next table shows how those benefits typically translate into measurable metrics.
How does AI eliminate network blind spots and enhance visibility?
AI removes blind spots by combining active and passive discovery with continuous telemetry correlation across endpoints, network devices and cloud services. Flow analysis reveals unexpected east–west traffic and large data transfers, while endpoint telemetry exposes process-level indicators that network-only tools miss. Automated asset discovery reconciles identity, device and application context into a single source of truth for security teams, enabling targeted monitoring and segmentation. The result is a richer topology that uncovers hidden connections and supports threat hunting across previously opaque areas of the estate.
Clearing blind spots naturally improves operational efficiency, which we cover next.
In what ways does AI improve operational efficiency in cybersecurity?
AI raises efficiency by automating repetitive triage, prioritizing alerts by risk score, and enabling playbook-driven responses that speed containment. Automated enrichment gathers related artifacts and builds incident timelines so analysts spend less time collecting data and more time resolving incidents. That lowers mean analyst handling time, lets smaller teams manage larger telemetry volumes, and preserves institutional knowledge through standardized playbooks. Over time these gains reduce cost per incident and increase SOC throughput.
Many organizations report meaningful drops in alert fatigue and false positives after adopting model-driven prioritization, freeing analysts for proactive threat hunting and strategic work.
Concertium’s core value — proactive threat mitigation, clear visibility, operational efficiency, compliance and end-to-end expertise — maps directly to these operational benefits. Teams evaluating options often start with a vulnerability scan or demo to validate visibility gains and measure MTTR improvements in a pilot.
How Does AI Observability Support Compliance and Risk Management?
AI observability strengthens compliance and risk management by automating continuous control checks, collecting audit-ready evidence, and prioritizing remediation by exposure. Telemetry mapped to controls enables automated reporting on configurations, access anomalies and control drift — reducing manual audit effort and surfacing gaps earlier. Risk-scoring algorithms combine vulnerability, exploit trends and asset criticality to guide remediation SLAs so teams address the highest-impact issues first. These capabilities help security and compliance teams show continuous adherence to policy and provide structured artifacts that speed auditor reviews.
The automated compliance and risk workflows below follow directly from how telemetry is translated into controls and remediation actions.
What role does AI play in automated compliance monitoring?
AI maps telemetry to compliance controls by turning events and state into control-relevant artifacts — access logs, configuration snapshots and evidence of enforcement. Rule mappings and pattern-detection models continuously validate control effectiveness and alert on drift when telemetry deviates. Automated reports bundle the relevant logs and concise context for each control exception, simplifying auditor review and remediation tracking.
Automated monitoring therefore feeds risk-based prioritization, helping teams focus remediation where it matters most.
How does AI-driven risk assessment reduce cybersecurity vulnerabilities?
AI-driven risk scoring reduces vulnerabilities by combining threat intelligence, vulnerability data, exploit trends and asset value into a single prioritization for each finding. That score helps teams focus patches, configuration changes and compensating controls on issues with the highest exploitation likelihood and business impact. Remediation playbooks can integrate with ticketing and patch systems to close the loop, and SLAs tied to risk tiers ensure timely action. The end result: fewer exposed high-value assets and clearer alignment between security activity and business risk reduction.
What Are Industry-Specific Applications of AI Cybersecurity Observability?
AI observability adapts telemetry, models and controls to sector risks and regulatory needs, delivering measurable gains in finance, healthcare, manufacturing and other regulated domains. Platforms tune detection to transaction patterns in finance, PHI protection in healthcare and OT/ICS behaviors in manufacturing. By aligning models with domain signals and compliance requirements, organizations get stronger detection coverage and faster, context-aware incident response. The subsections below outline use cases and outcomes for key industries.
Quick preview of industry focus areas covered here:
- Financial Services: Transaction anomaly detection, fraud reduction and regulatory reporting.
- Healthcare: PHI protection, anomalous access detection and audit-ready evidence.
- Manufacturing: OT/ICS asset visibility, process anomaly detection and safety-focused incident response.
How does AI observability enhance security in financial services?
In financial services, AI observability applies transaction-anomaly detection, monitoring of high-value systems, and enriched audit trails to detect fraud and insider misuse. Models analyze transaction patterns, session behavior and device signals to flag unusual transfers or credential misuse, while graph analytics uncovers coordinated fraud rings and lateral movement across systems. That reduces fraud dwell time, speeds reconciliation of suspicious activity for regulators, and supports clear reporting for compliance teams.
These targeted capabilities must be balanced with privacy and regulatory constraints — a topic we address for healthcare and manufacturing next.
What are AI benefits for healthcare and manufacturing cybersecurity?
In healthcare, AI observability concentrates on protecting patient data (PHI) and spotting abnormal access to electronic health records, with models tuned to clinical workflows to reduce false positives. Continuous evidence collection supports HIPAA-aligned audits and helps prioritize fixes where patient impact is highest. In manufacturing, observability extends into OT/ICS environments where unconventional telemetry and safety constraints require specialized sensors and anomaly models; AI can detect process deviations, unauthorized command sequences and segmentation breaches that risk production and safety. Both sectors gain prioritized remediation that balances safety, compliance and operational continuity.
These industry adaptations show how AI-enhanced observability can be tailored to operational and regulatory realities while retaining core benefits like reduced dwell time and improved triage.
When organizations are ready to act, Concertium offers an AI-Enhanced Advanced Observability service within its Collective Coverage Suite (3CS) to operationalize telemetry ingestion, ML-driven anomaly detection and SIEM integration — delivering prioritized alerts and evidence collection. Start with a consultation or pilot to validate visibility gains and measure reductions in MTTD and MTTR.
- Request a visibility assessment: Validate telemetry coverage and identify blind spots in a pilot.
- Run a vulnerability scan or pilot: Measure detection lift and operational impact.
- Adopt a prioritized roadmap: Align remediation with risk scores for immediate ROI.
These steps help teams move from evaluation to measurable improvement while keeping strategy and operations clearly separated, as described throughout this article.
Frequently Asked Questions
What types of organizations can benefit from AI-enhanced cybersecurity observability?
AI-enhanced observability benefits a wide range of organizations — from finance and healthcare to manufacturing and technology. Every sector faces distinct threats and compliance needs, so observability solutions should be tailored to operational context. For example, banks use AI for transaction-anomaly detection, while hospitals focus on protecting PHI. Properly tuned models and telemetry help organizations strengthen security and meet regulatory obligations.
How does AI observability integrate with existing security tools?
AI observability integrates with existing systems like SIEMs, XDR platforms and SOAR tools by ingesting telemetry and alert data and returning prioritized, enriched insights. Those integrations enable automated playbooks, streamlined incident management and more accurate detections. Augmenting current tools with AI-driven context reduces false positives and makes SOC workflows more efficient.
What challenges do organizations face when implementing AI-driven observability?
Common challenges include data silos, integration complexity and the need for skilled staff. Data silos limit visibility, while integrations can demand engineering effort and time. Organizations also need the right expertise to tune models and interpret AI outputs effectively. Addressing these gaps — through phased pilots, vendor partnerships or managed services — helps maximize observability benefits.
How can organizations measure the effectiveness of AI-enhanced observability?
Measure effectiveness using KPIs like mean time to detect (MTTD), mean time to respond (MTTR), and reduction in false positives. Track analyst workload, incident volume and time-per-incident to quantify operational improvements. Pilot projects that compare before-and-after metrics are an effective way to validate detection lift and ROI.
What role does threat intelligence play in AI-driven observability?
Threat intelligence enriches models with context about known malicious actors, indicators and tactics. Integrated feeds improve detection precision and help prioritize alerts tied to real-world threats. In short, threat intelligence sharpens AI’s ability to surface relevant, high-risk activity and keeps observability tuned to the evolving threat landscape.
Can AI observability help with compliance requirements?
Yes. AI observability automates continuous monitoring and evidence collection, mapping telemetry to controls and generating audit-ready artifacts. This streamlines compliance for frameworks like GDPR, HIPAA and PCI‑DSS, reduces manual audit burden, and helps teams remediate control gaps faster.
Conclusion
AI-enhanced observability gives organizations clearer, continuous insight across their environments so they can detect threats earlier and act faster. By combining rich telemetry with machine learning, teams reduce response times, cut false positives and improve operational efficiency — all while supporting compliance. If you’re ready to strengthen visibility and speed response, our AI-Enhanced Advanced Observability service can help transform your security posture. Explore our offerings to see how we can help you move from blind spots to prioritized, actionable intelligence.