Concertium XDR Solutions: Comprehensive Threat Coverage for Modern Businesses
Extended Detection and Response (XDR) brings together telemetry from endpoints, network, cloud, email and identity to detect, investigate, and automate responses—shortening breach dwell time while simplifying security for business leaders. This guide defines XDR, shows how it ingests and correlates cross-platform data, and explains why unified detection matters for resilience, compliance, and cost control. You’ll find a clear definition, a practical comparison to EDR, SIEM and MDR, a breakdown of core platform capabilities, and vertical guidance for Financial Services, Healthcare, Manufacturing, Retail and Government.
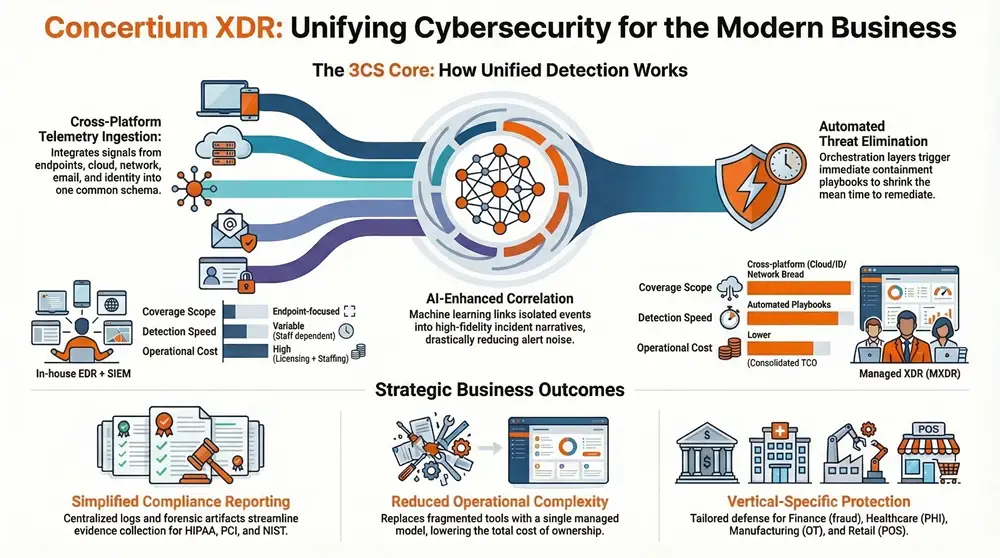
We also map how managed XDR—specifically Concertium’s Collective Coverage Suite (3CS) with AI-Enhanced Advanced Observability and Managed Detection and Response—turns those capabilities into operational coverage that closes observation gaps and speeds remediation. This is a practical resource for technical and non-technical stakeholders evaluating an XDR strategy that reduces risk, supports compliance, and aligns security with business priorities.
What is Extended Detection and Response?
Extended Detection and Response (XDR) is a unified cyber defense model that centralizes telemetry from multiple security domains, correlates events with analytics and threat intelligence, and automates investigation and response to narrow the window between detection and containment. XDR normalizes disparate signals—endpoints, network flows, cloud logs, email metadata and identity events—then links them into contextual incident narratives and applies analytics or playbooks to surface and prioritize high-fidelity incidents. The outcome: faster detection of multi-stage attacks, fewer false positives for analysts, and cleaner forensic trails that simplify compliance reporting. Seeing how XDR ties sources together explains why it’s the logical evolution beyond siloed EDR and legacy SIEM approaches.
XDR builds cross-layer context that single-source tools miss. The section that follows outlines the ingestion, normalization, correlation and orchestration steps that make unified threat detection possible.
How does XDR integrate endpoints, networks, cloud, email, and identity for unified threat detection?
XDR ingests telemetry from endpoints, network sensors, cloud APIs, email gateways and identity logs, then maps those signals to a common schema so correlation is possible. Ingestion pipelines parse and enrich data—adding user attribution, process lineage and geolocation—so analytics can join events into coherent incident timelines instead of isolated alerts. Correlation engines leverage rules, behavioral baselines and machine learning to reveal multi-step attack chains: an email-delivered payload, lateral movement on endpoints, and anomalous cloud activity. When the platform identifies high-confidence incidents, orchestration layers trigger automated containment or curator-approved playbooks for analysts—shrinking mean time to remediate while preserving forensic context for post-incident review.
Why are XDR Cybersecurity Benefits Essential for Business Owners?
XDR delivers measurable business value by improving detection accuracy, speeding response, and reducing operational complexity—together these lower breach risk and the total cost of ownership for security programs. For business owners, that translates into less downtime, fewer regulatory exposures and more predictable security spending because XDR consolidates visibility and removes duplicated tooling and effort.
XDR delivers several core business advantages:
- Enhanced detection: cross-source correlation exposes sophisticated, multi-stage attacks faster than single-source tools.
- Faster response: automated playbooks and prioritized incidents shorten containment time and limit business impact.
- Reduced operational complexity: unified telemetry and workflows cut analyst time spent on triage and switching tools.
- Compliance support: consolidated logs and contextual incident data simplify audit evidence collection and reporting.
Together, these benefits move security from reactive firefighting to predictable risk reduction. The table below compares in-house EDR/SIEM approaches with Managed XDR so decision-makers can see practical trade-offs.
Note: the following table summarizes typical deployment models to clarify coverage, detection speed and operational cost implications for business leaders.
For organizations without large in-house SOC teams, managed XDR often offers the best balance of broad coverage and operational efficiency. Next, we detail specific security and efficiency gains XDR delivers in day-to-day operations.
What enhanced security and efficiency advantages does XDR provide?
XDR reduces false positives and streamlines analyst workflows by surfacing prioritized, context-rich incidents that combine telemetry with threat intelligence so teams focus on verified threats. AI-driven models and behavioral analytics raise alert fidelity and suppress low-value noise, which reduces burnout and improves SOC throughput. Practically, organizations using XDR detect lateral movement and credential misuse earlier because cross-source linkages reveal suspicious sequences sooner. Those efficiency gains multiply when XDR is delivered as a managed service, providing 24/7 monitoring and response without the fixed costs and ramp time of building a large in-house SOC.
These operational improvements lead naturally into how managed XDR platforms—like Concertium’s Collective Coverage Suite—use AI-enhanced observability and MDR to make those gains operational.
How does Concertium’s Collective Coverage Suite Deliver an Integrated XDR Platform?
Concertium’s Collective Coverage Suite (3CS) pairs XDR principles with managed delivery: AI-Enhanced Advanced Observability, Managed Detection and Response (MDR), and Automated Threat Detection and Elimination all operate inside a single managed model. The platform covers end-to-end needs—cross-platform telemetry ingestion, AI/ML analytics to cut alert noise, and analyst-backed response to contain and remove threats. Deployments integrate with existing infrastructure and compliance programs, enabling continuous monitoring and evidence collection aligned with standards like NIST and ISO/IEC 27001:2022. The Managed 3CS model emphasizes hands-on partnership to accelerate time-to-value while sustaining operational continuity and audit readiness.
Below is a concise breakdown of the primary 3CS components and their role within an integrated XDR approach.
- AI-Enhanced Advanced Observability: collects and enriches cross-layer telemetry to build context for analytics.
- Managed Detection and Response (MDR): staffed analysts validate alerts, conduct investigations and execute containment.
- Automated Threat Detection and Elimination: playbooks and orchestration automate containment for routine or high-confidence incidents.
These elements combine into a cohesive operational model. The sections that follow describe the core components and explain how AI plus MDR improves detection and response.
What are the core components of Concertium’s XDR offering?
Concertium’s XDR offering within 3CS starts with AI-Enhanced Advanced Observability to gather and normalize telemetry across endpoints, network, cloud, email and identity—the foundation for cross-source correlation. Managed Detection and Response provides human analysts who validate high-confidence alerts, perform deeper hunts and coordinate remediation with your teams. Automated Threat Detection and Elimination applies curated playbooks and orchestration to contain incidents quickly while preserving forensic artifacts for post-incident analysis. Cross-platform coverage ensures detection isn’t limited to endpoint signals but includes network anomalies, cloud configuration drift and identity-based risk—reducing blind spots across hybrid environments.
Tying these components into a repeatable operational cadence produces a predictable, managed security posture that supports compliance and business continuity objectives.
How do AI-Enhanced Advanced Observability and Managed Detection and Response enhance threat detection?
AI-Enhanced Advanced Observability uses machine learning and statistical baselining to surface anomalies that rule-based systems can miss—subtle shifts in multi-user behavior or low-and-slow exfiltration across cloud APIs, for example. These models improve signal context—linking a suspicious process on an endpoint to concurrent anomalous cloud access and a risky email—raising alert fidelity and analyst confidence. Managed Detection and Response operationalizes those detections: analysts validate enriched alerts, pivot across telemetry, run containment playbooks and provide clear remediation steps to operations teams. The combined human+AI approach speeds containment while ensuring automated actions are appropriate—balancing velocity with accuracy.
These detection improvements directly inform the tool-comparison discussion below.
How Does XDR Compare to EDR, SIEM, and MDR?
XDR differs from EDR, SIEM and MDR mainly by scope, data sources and the end-to-end detection-to-response workflow. XDR is a cross-layer platform designed to correlate signals across domains rather than operate in a single domain. EDR focuses on endpoint telemetry and endpoint-centric prevention and response. SIEM collects logs for centralized search, analytics and compliance, often requiring significant tuning. MDR delivers managed analysts who investigate and respond, typically relying on the telemetry the provider can access. XDR combines broad telemetry ingestion with integrated analytics and automated playbooks to offer a more cohesive, context-rich detection and response lifecycle than pieced-together solutions.
The table below summarizes differences in data sources, primary function and recommended use cases for each approach.
For organizations with fragmented tools or limited analyst capacity, XDR’s centralized telemetry and automation combined with managed expertise often delivers the most efficient coverage. The next section offers guidance on choosing among these models.
What are the key differences in scope, data sources, and functions among XDR, EDR, SIEM, and MDR?
EDR delivers deep endpoint visibility and remediation controls but lacks native cross-layer correlation, which limits detection of attacks spanning email, cloud and network. SIEM centralizes logs for search and compliance but typically requires heavy parsing and tuning to produce timely detections. MDR brings human expertise to bear but can be limited by the telemetry available to the provider. XDR unifies these strengths: it ingests broad telemetry, applies analytics to correlate events, and offers orchestration for both automated and human-driven response—making it well suited to organizations seeking an integrated, efficient security operations model with stronger detection coverage.
Choosing the right model depends on existing telemetry, internal staffing and the organization’s tolerance for operational complexity. Next we map XDR to industry-specific risks and compliance needs.
What Are the Industry-Specific Applications of Concertium XDR?
XDR looks different by vertical. Mapping top risk drivers to specific XDR capabilities helps security and business leaders prioritize sensors, analytics and controls for maximum impact. Financial Services needs transaction and fraud telemetry combined with identity analytics to catch account compromise early. Healthcare prioritizes patient-data protection and audit trails to meet HIPAA. Manufacturing requires OT/IT visibility to detect lateral movement that reaches operational systems. Retail focuses on POS and transaction telemetry to protect cardholder data and meet PCI DSS requirements. Government and critical infrastructure need strong data classification, identity assurance and continuity planning to satisfy NIST and sector mandates.
The table below maps common industry risks to XDR capabilities and compliance impact to guide vertical-specific configurations.
This vertical mapping helps security architects prioritize sensor placement, analytic models and playbooks. The following examples show how XDR addresses specific compliance and operational needs.
How does XDR address security and compliance needs in Financial Services, Healthcare, Manufacturing, Retail, and Government?
In Financial Services, XDR links anomalous logins to transaction irregularities to surface likely account takeover events—enabling rapid holds or reversals while preserving forensic context for regulators. Healthcare benefits when XDR preserves access logs and file-change histories tied to patient records, simplifying breach investigations and HIPAA reporting. Manufacturing uses combined IT/OT telemetry to spot lateral movement that could affect production systems, enabling containment before physical processes are disrupted. Retail leverages XDR to detect abnormal POS traffic and unusual outbound connections that suggest data exfiltration—supporting PCI investigations. Government agencies use XDR to centralize classification-aware logging and enforce privileged-access playbooks that align with NIST and other mandates.
These examples show practical deployment patterns and lead into considerations about vendor selection and managed engagements.
Why Choose Concertium for Your Managed XDR Services?
Concertium frames its managed XDR services around hands-on partnership, end-to-end capability and compliance experience—designed to accelerate deployment and sustain effective security operations. With decades of experience protecting technology environments, our approach spans strategy, infrastructure, security controls and ongoing management, and includes AI-driven observability to improve detection and response.
Concertium’s value is driven by three core differentiators:
- Hands-on partnership that reduces implementation risk and speeds time-to-value.
- End-to-end services from strategy through managed operations and post-breach support.
- AI-driven observability paired with MDR to provide continuous detection and validated response.
These differentiators translate technical capabilities into business outcomes—shorter breach lifecycles and stronger compliance posture. The subsections below outline partnership benefits and accreditations that demonstrate operational credibility.
How do Concertium’s experience, end-to-end capabilities, and hands-on partnership benefit your cybersecurity strategy?
Partnering with Concertium minimizes implementation friction by covering strategy, infrastructure setup, security control deployment and managed operations—helping customers realize monitoring and response capability faster than building equivalent in-house functions. Continuous tuning and managed SOC operations keep analytics effective as environments change, while hands-on collaboration with client teams shortens remediation cycles and preserves institutional knowledge. Our managed model converts variable staffing costs into predictable subscriptions and gives access to specialized skills and playbooks many organizations lack internally—reducing operational risk and improving long-term security posture.
What accreditations and client success stories demonstrate Concertium’s expertise?
Concertium maintains a compliance-focused posture and follows recognized frameworks that guide our operations, including SOC 2, PCI DSS, NIST, ISO/IEC 27001:2022 and relevant FTC practices. These credentials reflect capability in audit readiness, evidence preservation and controlled change management—important for regulated industries and public sector clients. We pair accredited processes with a consultative delivery model (3CS) to turn compliance requirements into operational controls and continuous monitoring practices that lower audit cost and complexity.
By combining accredited processes with managed XDR delivery, Concertium provides both technical coverage and the governance controls auditors expect, making it easier to demonstrate compliance while maintaining robust detection and response.
Frequently Asked Questions
What types of businesses can benefit from XDR solutions?
XDR benefits a broad range of organizations—Financial Services, Healthcare, Manufacturing, Retail and Government among them. Each sector faces distinct challenges: fraud and regulatory oversight in finance, patient-data protection in healthcare, OT risk in manufacturing, POS exposure in retail, and continuity requirements in government. XDR helps these organizations improve threat detection, streamline incident response and support industry-specific compliance, strengthening overall security posture.
How does XDR improve incident response times?
XDR speeds incident response by automating detection and response workflows across multiple domains. By correlating data from endpoints, networks and cloud services, XDR highlights high-confidence threats and prioritizes them for action. Automated playbooks enable rapid containment and remediation, reducing mean time to respond (MTTR) and freeing security teams to focus on complex investigations.
What role does AI play in XDR solutions?
AI is central to modern XDR. Machine learning analyzes large volumes of telemetry to find patterns and anomalies that rule-based systems can miss. AI-driven analytics prioritize alerts by severity and context, lowering false positives and surfacing high-fidelity incidents. AI also automates routine tasks, allowing analysts to spend time on strategic work and improving overall operational efficiency.
Can XDR solutions integrate with existing security tools?
Yes. XDR is designed to integrate with existing security investments. It can ingest data from EDR, SIEM and other tools to provide a unified view of threats across your environment. That interoperability lets organizations preserve current workflows while gaining the cross-source correlation and automation XDR enables.
What are the cost implications of implementing XDR?
While initial investment varies, XDR often reduces long-term costs by consolidating multiple tools, lowering licensing overhead and reducing the need for large in-house teams. Automated detection and response decrease time spent on incidents, which limits operational disruptions and associated costs. For many organizations, managed XDR delivers predictable subscription pricing and lower total cost of ownership over time.
How does XDR support compliance with regulations?
XDR supports compliance by centralizing logs and contextual data needed for audits and incident reporting. Consolidated telemetry and preserved forensic artifacts simplify evidence collection and reporting for regulations like HIPAA, PCI DSS and NIST frameworks. Automated monitoring and documented playbooks also help demonstrate an organization’s commitment to maintaining a robust security posture.
Conclusion
Concertium’s XDR solutions give organizations broad, practical threat coverage—improving detection accuracy, accelerating response and reducing operational complexity. That unified approach supports compliance and ties security activities to business objectives, helping create a more resilient environment. With managed XDR, you gain expert partners, proven processes and advanced technology to reduce risk and protect critical assets. Learn how our tailored solutions can strengthen your cybersecurity posture today.